In an earlier thread, I discussed using static configuration files in a virtual host to automate configuration of your users’ email clients, with techniques that will work with Thunderbird, Outlook, and compatible email clients. One notable limitation of that method is that it does not work for iOS/OSX mail, so your Apple users will still need to configure their mail clients manually.
This content has been moved to the wiki: https://wiki.nethserver.org/doku.php?id=email_autoconfig_module
Web forms
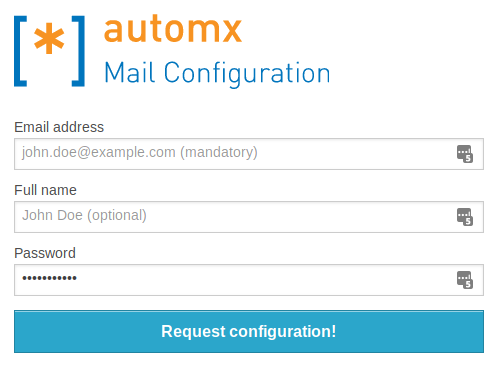
Now that your server will generate and sign the .mobileconfig files, you need to give your users a way to get those files. You’ll do that by giving them a web form into which they’ll enter their name, email address, and password, and click to download the profile. Automx provides such a form, or you can integrate your own into whatever web page you like.
automx-web
To install the default form, simply run
yum --enablerepo=danb35 install automx-web
This package includes forms in English and German; you’ll need to choose which one you want to present to your users. To use the English form, do:
cd /usr/share/automx
ln -s index.html.en index.html
Now, when your users visit autoconfig.yourdomain, they’ll see a form that looks like this:
Custom web form
If you don’t want the automx branding for your users, and/or you just want to put this into another page, you simply need to add the following HTML code:
<form action="/mobileconfig" method="post">
<input type="hidden" name="_mobileconfig" value="true" />
<label for="emailaddress">Email address</label>
<input name="emailaddress" id="emailaddress" type="email" placeholder="john.doe@example.com (mandatory)">
<label for="cn">Full name</label>
<input name="cn" id="cn" type="text" placeholder="John Doe (optional)">
</span>
<label for="password">Password</label>
<input name="password" id="password" type="password" placeholder="Password (optional)">
</span>
<input type="submit" value="Request configuration!" />
</form>
Of course, you can adjust styling, tool tips, etc. to suit your website. The look is up to you, but the input names have to stay the same.
TO DO
- Test, test, test
- See if I can get LDAP working as expected
- Integrate the .mobileconfig form into the server-manager (or, better yet, into the user-manager that doesn’t exist yet)
- Figure out why signing .mobileconfig files isn’t including the full certificate chain in the profile. This is causing the profiles to be marked as “unverified”.

 :
: