Hi all,
need your advise to stop SMTP relay in my production box.
Doubt it is open for SMTP relay.
Advise me the steps…
No, Neth isn’t an open SMTP relay. What makes you think it is?
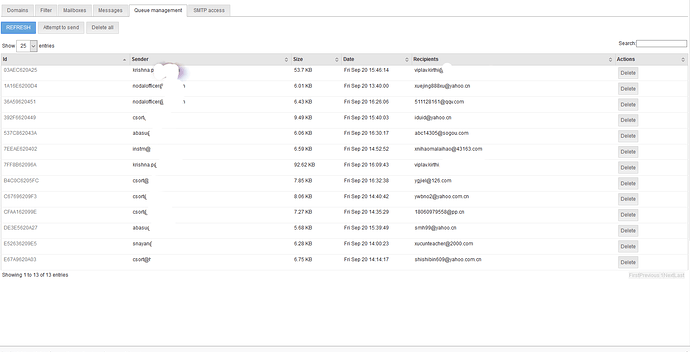
Am seeing unknown mails being sent from my server GUI (queue management).
Correct me
Not quite “open”…
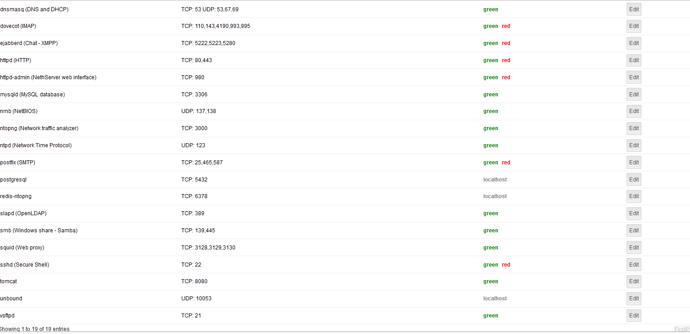
NethServer acts as a relay for some networks (green) and if something is enabled.
@bainwave can you verify from queue or log which is the ip sending messages and if any user is used for submitting?
Maybe you have a mass mailing worm inside your LAN and the relay is filtering (maybe) the messages …
It acts as a relay for green networks, but (by default) it requires authentication for any relaying.
@pike
Please bear with me… will update once i reach office…
I don’t have access to any SMTP relay configuration to verify.
Also: would you please describe what is your current setup?
Where is NethServer into network topology, what are it’s roles and what are services that it provides.
@pike
how do i show SMTP relay configuration to verify?
My NethServer is behind Fortigate firewall and in a LAN with 10 other servers and its roles basically email
Please find the images shows about the services and spam mails being sent from my server.
Help me
As @dan wrote before
as default setting, Nethserver do not act as SMTP relay for no one, except the users of the server
Also, i am assuming that your server is acting as email and webmail server. No websites of any kind.
A little checklist for “sanitize” the situation. Do not consiter it complete.
- If not already, enforce secure password policy ( Password policies, Strong password policy for Users)
- Change root password and if possible any of other administrative users (by NethServer perspective)
- Keep note the new password and of everything you are going to change from the next sections
- Check “Trusted Network” and remove any public subnet or address who should not be here
- Into “Email”, tab SMTP Access, ensure the list “Allow relay from IP addresses” is empty or only with ip addresses you choose to relay and uncheck the “advanced options” both for relay for trusted network and authentication on port 25.
- Edit: Into Email, tab Mailboxes, uncheck “Allow unencrypted connections” if enable.
- If not installed or enable, install or activate rSpamd
If all these settings are as described, i have to assume that someone found a password of one of your users, or one of your system into “Allow relay from IP addresses” list is compromised.
So pick one: remove entries from “Allow relay from IP addresses” or change all the users password.
Also: i am a Linux total n00b, there’s should be a way from shell to list all the ip addresses that are connected to a port or a service, but i don’t know which is.
And if the Fortigate is correctly configured and allows SMTP connections to internet only from NethServer, a computer into the lan could be coulprit for sending spam via nethserver using cached username and password into mail client or browser.
Summoning @support_team for more suggestions
@bainwave any news?
@pike.
Followed your suggestions, observed the situation under control.
Thanks for the suggestion.
Will observe for a couple of days and will let you know.
My server edition is 6.9 final. Planning to upgrade with the help of upgrade tool, but failed.
Now am planning to move the mailboxes from 6.9 to new server with 7.6 version installed.
Please let me know if you have any thoughts on it.
Thanks in advance
Version was a quite important information… And this should not be “6.9”, but 6.10, if it’s fully updated.
I don’t know if the upgrade tool (i don’t know if it was @davidep which posted about it) may receive interesting inputs from your experience…
@pike
You are right it is 6.10 but not 6.9.
Any how, now I have the latest version VM, help me out to migrate the existing mail boxes in 6.10 to new server 7.6
–
Bain
I have no experience in migration, therefore i cannot help you for this task. IMVHO should open another support topic.
Next step: how’s going the modified setup? Blocking the possibly compromised settings can stop the flow, but don’t solve the effective problem. Which, until now, is not know for the community.
@pike
This is getting interested day by day…
Although 90% of the issue fixed am still observing couple of machines in my network sending mails.
Getting checked for malware / virus infection in their machines today and will post the updates ASAP.
I hope that the epuration of bad software keeps proceeding, if the 90% is fixed, maybe some passwords (or crapwords) needs to be changed for safety.
Did you removed any host/subnet from Trusted networks and/or Allow relay from IP addresses?
About a year later i think that @bainwave should have solved the issue.
Or changed job location for something “a lot better” 
@pike,
I think I fixed the issues as per the snapshot… by disabling the two options at the bottom
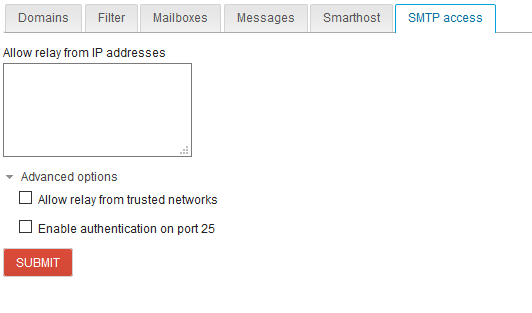
Now you may close this issue.
Thanks for reminding me after a year