Hello,
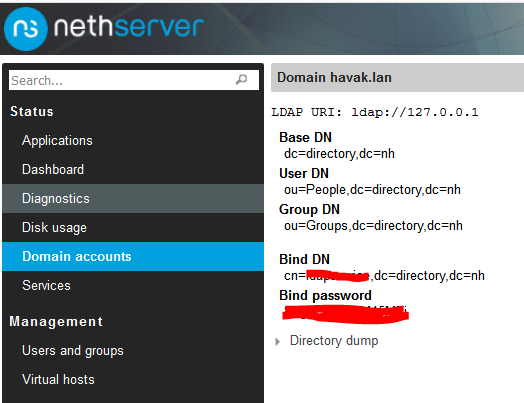
I have been trying to access the LDAP server of my Nethserver installation without success. I have done a clean install of Nethserver, created an OpenLDAP server and made some test users. If I access LDAP from the server itself (localhost) it seems to be fine, but if any other machine on the network (green) attempts to connect it fails. I think it may be as simple as allowing external connections to the LDAP server. From what I can tell the service and ports are open to my green network.
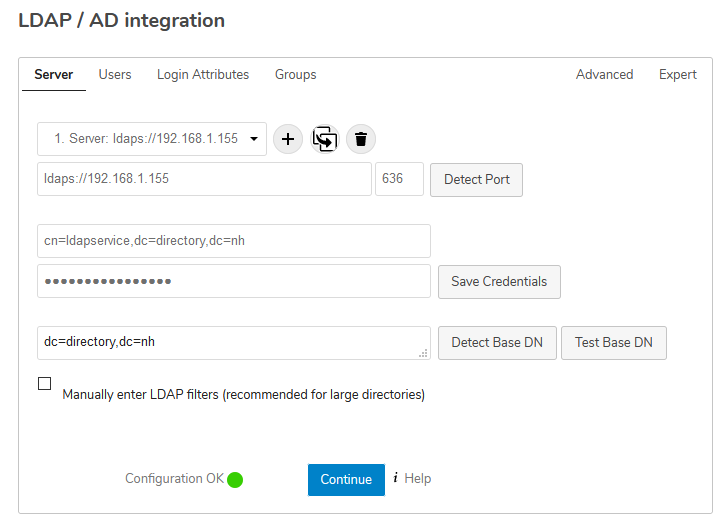
Ultimately what I am trying to do is have a user database on Nethserver be available to authenticate users from several network devices including a Nextcloud instance running on another machine. When I copy the LDAP settings from the Nextcloud instance running on the Nethserver itself to another machine on the network running Nextcloud the connection is lost though of course it works perfectly on the server (Nethserver) itself.
Is there a default or obvious setting I am missing to allow connections from other machines on the green network?