Thank Stefano, it what I understood by reading your post : Best Way of Updating PHP... or not
but I wasn’t sure
Also I could put the CVE list, put it’s truly long just to name a few
PHP : CVE-2006-7243, CVE-2010-2094, CVE-2010-2950, CVE-2010-3436, CVE-2010-3709, CVE-2010-3710, CVE-2010-3870, CVE-2010-4150, CVE-2010-4156, CVE-2010-4409, CVE-2010-4645, CVE-2010-4697, CVE-2010-4698, CVE-2010-4699, CVE-2010-4700, CVE-2011-0421, CVE-2011-0708, CVE-2011-1092, CVE-2011-1148, CVE-2011-1153, CVE-2011-1464, CVE-2011-1466, CVE-2011-1467, CVE-2011-1468, CVE-2011-1469, CVE-2011-1470, CVE-2011-1657, CVE-2011-1938, CVE-2011-2202, CVE-2011-2483, CVE-2011-3182, CVE-2011-3267, CVE-2011-3268, CVE-2011-3379, CVE-2011-4566, CVE-2011-4885, CVE-2012-0057, CVE-2012-0781, CVE-2012-0788, CVE-2012-0789, CVE-2012-1823, CVE-2012-2143, CVE-2012-2311, CVE-2012-2335, CVE-2012-2336, CVE-2012-2386, CVE-2012-2688, CVE-2012-3365, CVE-2012-3450, CVE-2012-6113, CVE-2012-1823, CVE-2013-1635, CVE-2013-1643, CVE-2013-4113, CVE-2013-6712, CVE-2014-0207, CVE-2014-0237, CVE-2014-0238, CVE-2014-3515, CVE-2014-3981, CVE-2014-4049
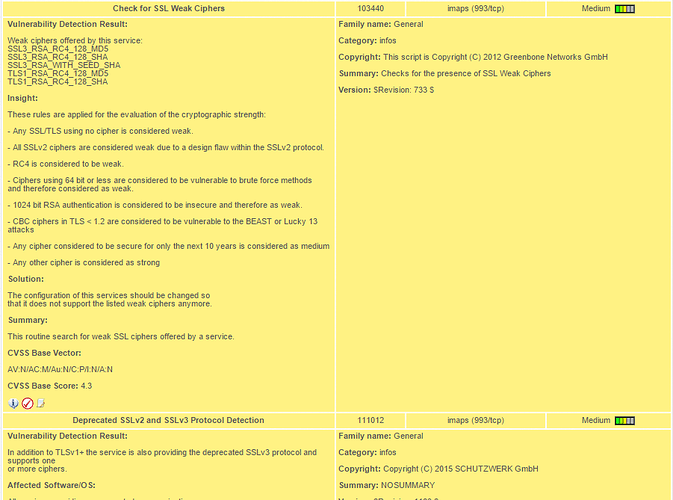
SSL : CVE-2007-1858, CVE-2013-4353, CVE-2013-6449, CVE-2013-6450, CVE-2014-0076, CVE-2014-0160, CVE-2010-5298, CVE-2014-0195, CVE-2014-0198, CVE-2014-0221, CVE-2014-0224, CVE-2014-3470, CVE-2015-0292, CVE-2014-3505, CVE-2014-3506, CVE-2014-3507, CVE-2014-3508, CVE-2014-3509, CVE-2014-3510, CVE-2014-3511, CVE-2014-3512, CVE-2014-3513, CVE-2014-3566, CVE-2014-3567, CVE-2014-3568, CVE-2014-5139, CVE-2010-5298
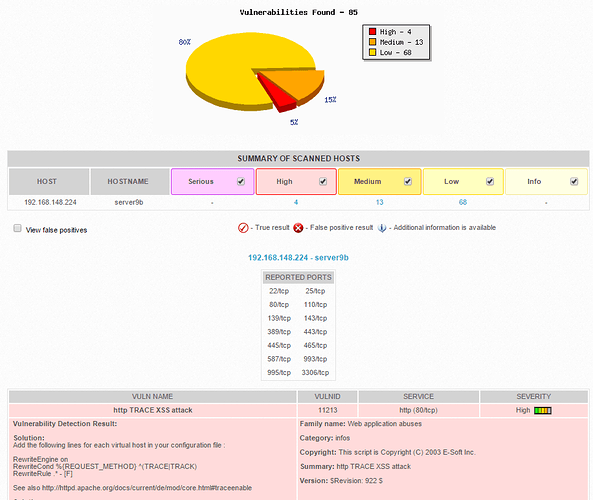
APACHE : CVE-2003-1567, CVE-2004-2320, CVE-2009-3560, CVE-2009-3720, CVE-2010-0386, CVE-2010-1452, CVE-2010-1623, CVE-2010-2068, CVE-2011-3368, CVE-2011-3607, CVE-2011-4317, CVE-2012-0021, CVE-2012-0031, CVE-2012-0053, CVE-2012-0883, CVE-2012-2687, CVE-2012-4557, CVE-2013-1862, CVE-2013-1896, CVE-2013-5704, CVE-2014-0118, CVE-2014-0226, CVE-2014-0231
RC4 : CVE-2013-2566, CVE-2015-2808