Ubuntu 19.04 (gnome)client ad nethserver join
Ps: on your Linux desktop client machines put the ip dns servers to nethserver ad container (192.168.7. 40) and the second dns (8.8.8.8), next edit the file resolve. conf, from terminal type
nano /etc/resolv.conf
Search ad.xyz.local
And save this file and reboot your pc client…
Ubuntu client: (ver 18.04 / 18.10 / 19.4)
Open terminal,
Install Required Packages
sudo apt update sudo apt-get -y install realmd sssd sssd-tools samba-common krb5-user packagekit samba-common-bin samba-libs adcli ntp
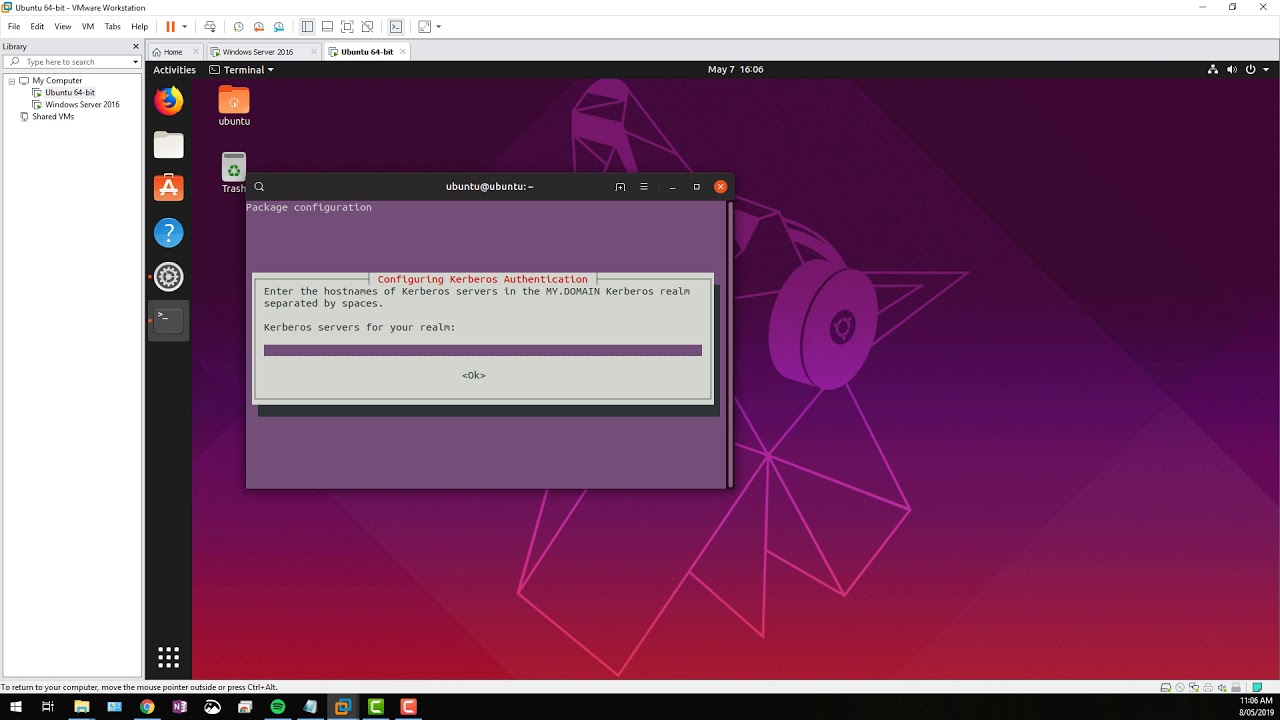
Kerberos Authentication
AD.XYZ.LOCAL
OR IF ASKED
SERVER.AD.XYZ.LOCAL
Change adapter to enter virtual environment (No internet access from here).
sudo realm join ad.xyz.local -U administrator -v (respect all the spaces as i did, otherwise the join will fail)
Setting up realmd: (To discover and join windows domain)
sudo vi /etc/realmd.conf
…
[users]
default-home = /home/%D/%U
default-shell = /bin/bash
[active-directory]
default-client = sssd
os-name = Ubuntu Desktop Linux
os-version = 18.10 [service]
automatic-install = no
[ad.xyz.local]
fully-qualified-names = no
automatic-id-mapping = yes
user-principal = yes
manage-system = no
…
Join the Ubuntu machine on the AD domain: (Kerberos) sudo kinit Administrator@AD.XYZ.LOCAL
------------------------------------------------------------in case--------------------------------------------------------------------
Error: Cannot contact any KDC for realm while getting initial credentials
I’ve been testing FreeIPA on a small network of CentOS 7 hosts (all virtual machines running in VirtualBox on a host-only network). After installing the IPA server on one host and creating the realm (ad.xyz.local), I installed the IPA client on one of the other hosts and tried running kinit :
# kinit admin kinit: Cannot contact any KDC for realm 'ad.xyz.local' while getting initial credentials
Searching for that error brought me to Kinit won’t connect to a domain server. Although that did not describe the same issue, it did point me to the /etc/krb5.conf file. The realms section looked like it was missing something:
[realms]
AD.XYZ.LOCAL = {
pkinit_anchors = FILE:/etc/ipa/ca.crt
}
I added a kdc attribute:
[realms]
AD.XYZ.LOCAL = {
kdc = prospero.osric.net:88
pkinit_anchors = FILE:/etc/ipa/ca.crt
}
No restart of any service was necessary. I ran kinit again and it worked:
# kinit admin Password for admin@AD.XYZ.LOCAL:
According to the krb5.conf documentation on realms:
kdc
The name or address of a host running a KDC for that realm. An optional port number, separated from the hostname by a colon, may be included.
I’m a Kerberos novice, but that seems like a necessary property. I’m not sure why the IPA client setup did not include it. I have a few more virtual machines to install the client on, so I’ll soon find if that behavior is consistent on subsequent installations.
Password for Administrator@ad.xyz.local:
Setup homedir auto-creation for new users:
sudo vi /etc/pam.d/common-session
…
session required pam_unix.so
session optional pam_winbind.so
session optional pam_sss.so
session optional pam_systemd.so
session required pam_mkhomedir.so skel=/etc/skel/ umask=0077
…
Final Check: Restart the machine and try to login using the Ubuntu graphical login by domain user and password. xyz\user (example) (HOME\sarah) and sarah password, like on windows
and tanan
okokokokokokokokokookok
video inspired
extra step (not tested yet)
accessing windows file shares using samba
sudo apt-get install samba
sudo apt-get install winbind
mapp remote share
smb://192.168.2.74(nethserver ad ip container)/share1/
smb://192.168.2.74/ HomeDir$
To test roaming user files and folder creation
Test 1
https://github.com/aadityabagga
Test 2
etc/sssd.conf,
/etc/sssd/sssd.conf
override_homedir = /var/lib/nethserver/home/%f
I’ve changed %f with %u bacause %f is expanded as user@domain while %u is expanded as user without @domain
override_homedir = /var/lib/nethserver/home/%u
Then I’ve created a new user in RSAT/ADUC then I logged with that new user in Windows 7.
All seems to work correcly!
Ciao