@carsten
Hello Carsten
For another german friend from this Forum I have set up what you want:
A hosted NethServer with static IP.
An OpenVPN connection as RoadWarrior (For Management) with Port 1194 (Standard OpenVPN)
An OpenVPN Site2Site VPN. The Site2Site is ALWAYS initialized from the client side (Due to dynamic IP makes more sense), but also for security reasons. No one at the hoster can initialize any form of VPN to a dynamic IP, especially as the destination changes daily… 
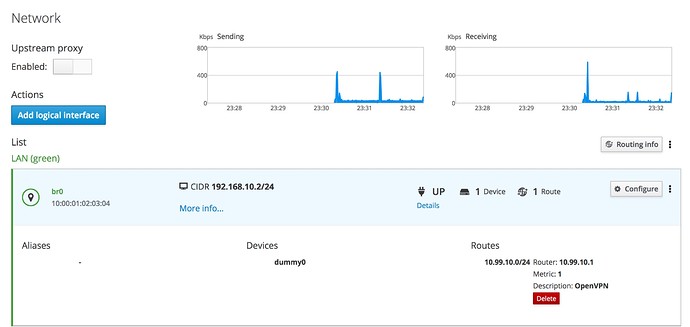
You need to set up a typical NethServer (Over Centos 7 minimal), and do not forget to add a bogus NIC, as “LAN” or endpoint of the VPN. See this, but adapt the IPs and such:
https://wiki.nethserver.org/doku.php?id=virtual_network_interface&s[]=dummy
The HowTo works very well, but I adapted a lot as to my requirements…
In your case, your NethServer at your site would init the OpenVPN Site2Site as a Client, the Server is the hosted NethServer.
OpenVPN site2site are never equals, unlike IPsec, where both are equals and both can init a VPN connection… In OpenVPN site2site VPNs, one side is always the server (waiting for a client to connect) and the other side is a Client (initializes the connection).
As additional motivation: The external NethServer has 10 of 10 points when doing a mailcheck! 
On the NethServer, I use users like smtp-client1 for the smarthost function. (Outgoing mails from your local site)
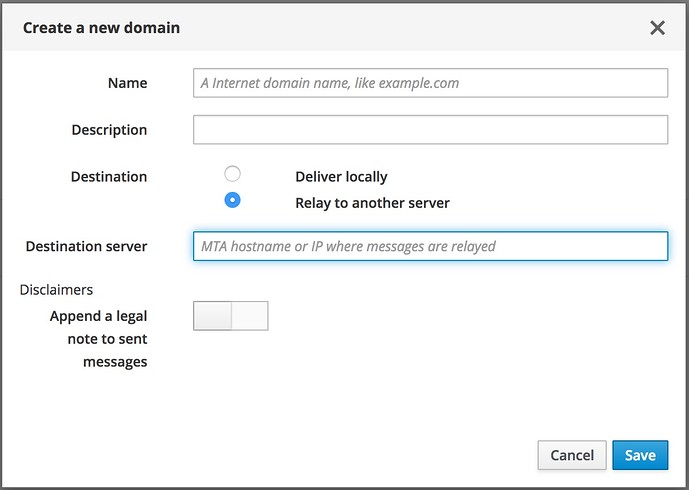
For incoming (From Internet to your local NethServer) there are a few options, most elegant and simplest would be NethServer forwarding mails per Domainname to the specified IP…
TIP: Just forward the ports you need. If you forward all, you’ll just get a lot of unwanted and unneeded traffic, making your internet slower for no real reason. Ports are added easily later, if needed!
Hope this helps
My 2 cents
Andy
Incoming: