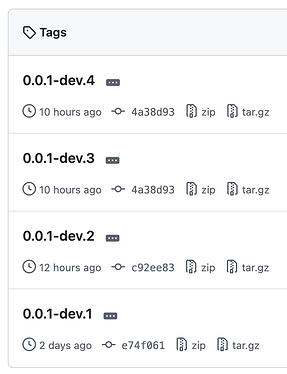
ns8-ssh-access-manager v0.0.1-dev.6
First public beta release of ns8-ssh-access-manager, a NethServer 8 module for centralized SSH key auditing and lifecycle management.
Overview
Managing SSH access at scale is a common blind spot in many infrastructures.
On a typical fleet of Linux servers, SSH `authorized_keys` files are:
- scattered across multiple machines and user accounts
- manually managed (e.g. via `ssh-copy-id`)
- rarely audited
- almost never rotated
Over time, this leads to:
- orphaned keys when users leave a team
- uncontrolled access persistence
- lack of visibility on who can access what
- potential security risks and compliance issues
ns8-ssh-access-manager was developed to address these problems by providing:
- centralized visibility
- continuous auditing
- controlled key lifecycle management
The goal is simple: make SSH access **observable, auditable, and enforceable**.
Added
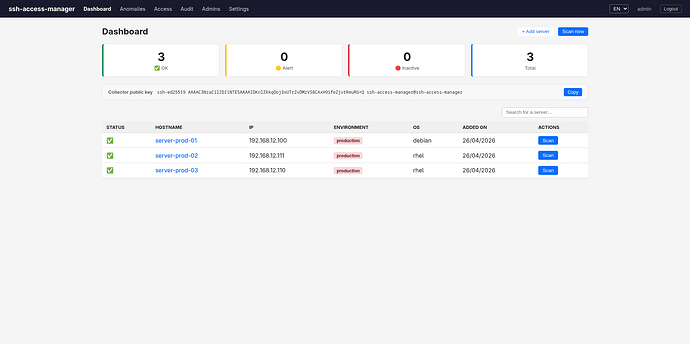
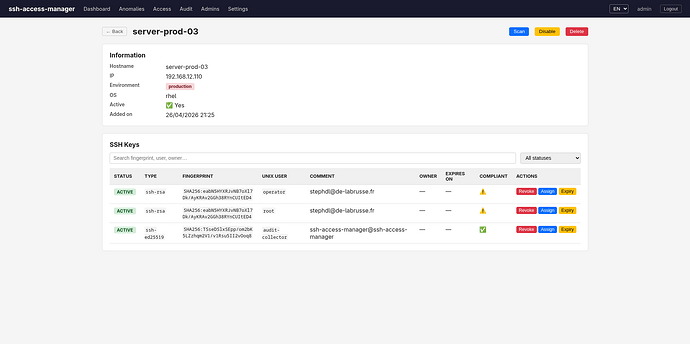
- Centralized web interface to view SSH authorized_keys across all managed servers
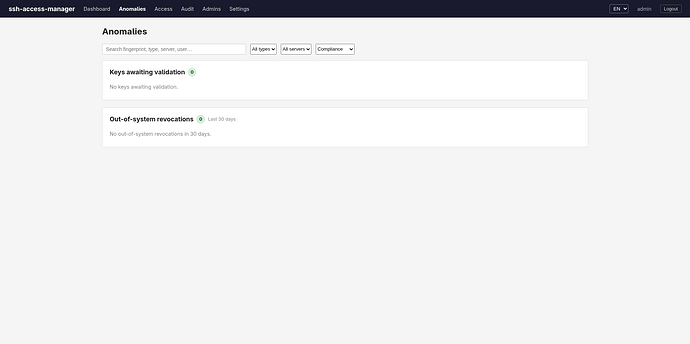
- Anomaly detection system:
- Detects keys added or removed outside the platform (e.g. ssh-copy-id, manual edits)
- Generates critical alerts on unexpected changes
- ANSSI BP-099 compliance checks:
- Flags weak SSH keys (RSA < 4096 bits)
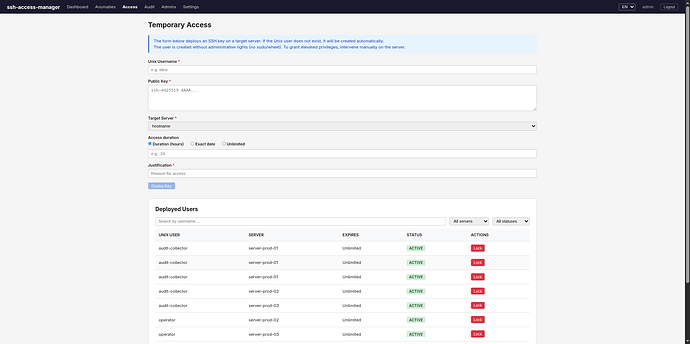
- SSH key lifecycle management:
- Key creation with expiration date
- Mandatory justification field
- Automatic key revocation at expiry
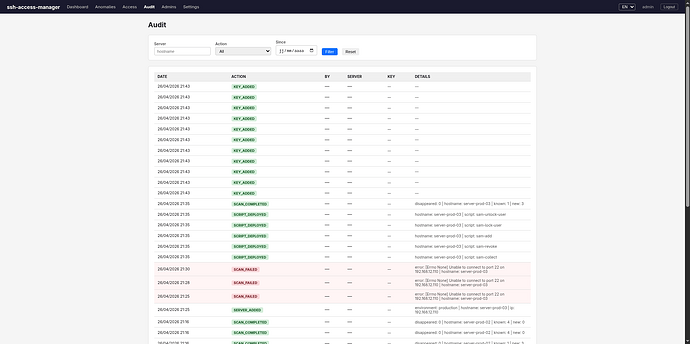
- Audit logging:
- Tracks key additions, revocations, and script deployments
- Automated provisioning system:
- Remote deployment of audit scripts
- Idempotent server setup
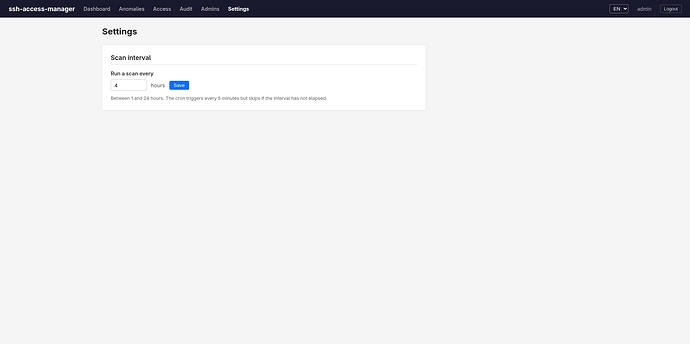
- Periodic background scans with configurable interval
- Ability to manage SSH keys on the host running the module itself
Security
- No root access required for standard operations
- Dedicated restricted user (
audit-collector) created on managed hosts - Controlled sudo access limited to five scripts:
- sam-collect
- sam-add
- sam-revoke
- sam-lock-user
- sam-unlock-user
- Script integrity ensured via hash-based updates
Installation
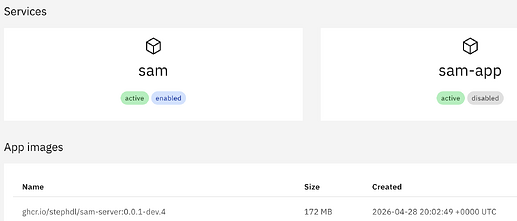
add-module ghcr.io/stephdl/sam:0.0.1-dev.7 1
Then configure the module from the NethServer 8 Software Center.
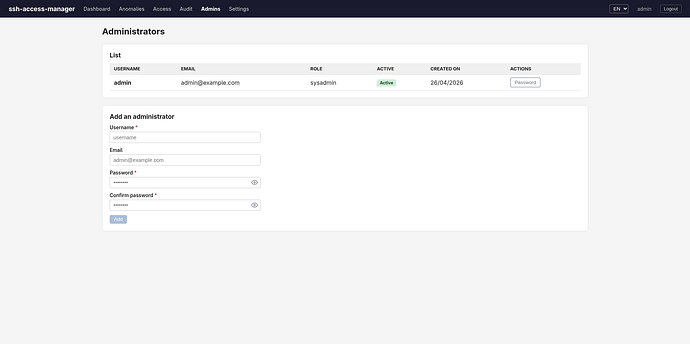
The default login is admin/admin
SMTP settings are automatically inherited from the system configuration.
Provisioning
runagent -m sam1 ../bin/provision-server \
--hostname server-prod-01 \
--ip 192.168.1.100 \
--user root \
--env production \
--os rhel
Options
| Option | Default | Description |
|---|---|---|
| –hostname | required | Server hostname |
| –ip | required | Server IP address |
| –user | root | SSH user |
| –env | production | Environment (production, staging, dev) |
| –os | other | Target OS (rhel, debian, ubuntu, alpine) |
Workflow
- Initial scan imports all existing keys as PENDING_REVIEW
- Alerts are generated for unknown keys
- Administrator reviews and validates or revokes keys
- Continuous scans detect and report any external changes
Known Issues
- Beta release, APIs and data model may change
- Limited OS support detection
- No high availability support
- Notification system is still a work in progress
Disclaimer
- This is a beta release and should be tested on non-production environments
- Use on test servers is strongly recommended before any production deployment