Greetings to the community.
I would like to put my situation into discussion with the expectation of some ideas:
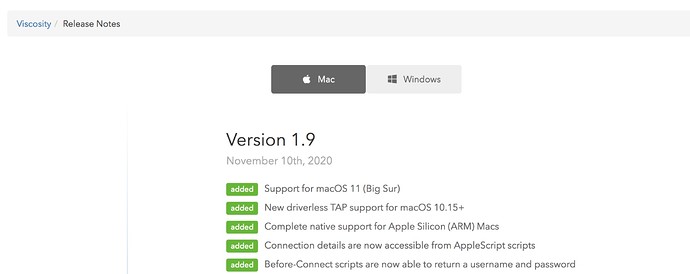
I have been running a nethserver for local sharing for some time now. Everything works as it should. For homeoffice users we use the connection via OpenVPN on the nethserver. This also works fine. Due to the arrival of a new Mac laptop user running “Big Sure” and CPU M1, I am dealing with its connection from home. The OpenVPN client application Tunnelblick is not currently supported on OS “Big Sur” … and who knows if it will ever be … everything is in beta testing … Apple applies restrictions for loading drivers in “Big Sur”. So we cannot solve this path yet. I implement a parallel VPN tunnel on the Mikrotik router. I set it up on technology (L2TP / ipsec) and I’m starting to test the connection and availability of services on the LAN through L2TP / ipsec. Connection and availability is OK, but sharing on a nethserver (smb) is broken. I will specify the situation … sharing for clients directly in the LAN - tested OK. Sharing for clients via OpenVPN (nethserver service) is also OK. Nethserver sharing for clients connected to an L2TP / ipsec VPN - no Samba response (or authorization prompt). Sharing to other servers in the same LAN (Windows server 2012R2), to Synology NAS also OK (works via L2TP / ipsec, also OPenVPN).
I don’t understand what makes it different for nethserver / samba from Synology / NAS (samba) and Windows server sharing …
I have some connection with setting up MTU and encrypting encrypted packets and setting up ethernet / bridge / smb on the nethserver. I don’t know how to tune on the nethserver side.
Comparison of what I see -
Synology (Linux) eth: eth0: <BROADCAST, MULTICAST, UP, LOWER_UP> mtu 1500 qdisc mq state UP qlen 532
Nethserver:
em1: <BROADCAST, MULTICAST, UP, LOWER_UP> mtu 1500 qdisc pfifo_fast master br0 state UP group default qlen 1000
br0: <BROADCAST, MULTICAST, UP, LOWER_UP> mtu 1500 qdisc noqueue state UP group default qlen 1000
Thanks for any idea.
Viktor
NethServer release 7.9.2009 (final)
kernel 3.10.0-1160.11.1.el7.x86_64
Samba version 4.10.16