NethServer Version: 7.9
Module: ThreadShield
I have a question to better understand the behavior. I have had Thread Shield disabled for a while and only now re-enabled.
A look at the log files shows me:
Oct 10 09:33:42 ns-srv01 kernel: Shorewall:blacklst:DROP:IN= OUT=eth0 SRC=45.157.178.109 DST=144.217.105.209 LEN=700 TOS=0x00 PREC=0x00 TTL=64 ID=38601 DF PROTO=TCP SPT=2202 DPT=37480 WINDOW=227 RES=0x00 ACK PSH URGP=0
In my understanding, my server (45.157.178.109) tries to connect 144.217.105.209 an port 2202.
I can’t understand why it does that, I don’t have a dedicated connection set up or can’t remember. The port is identical to my customized SSH port. Coincidence?
I also can’t understand why Thread Shield blocks outgoing connections from my server IP.
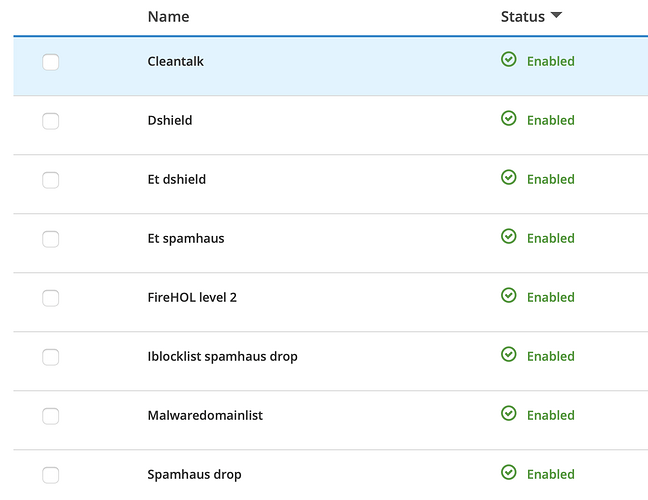
My thread shield configuration
Information about the DST-IP
144.217.105.209 IP Address Information
|ISP|Hop Off A Cloud LLC|
| — | — |
|Usage Type|Data Center/Web Hosting/Transit|
|Hostname|ip209.ip-144-217-105.net|
|Domain Name|countryconnections.net|
|Country||
|City|Montreal, Quebec|
Am I missing something that is actually obvious?
Best regards, Marko
Ps: on the Analysis site, I can see the opposite information.