Hi all,
I’d like to get your opinion.
I use OpenVPN as a tunnel to connect my two servers so that all networks can be reached.
The whole thing works very well.
What I have noticed is that the speed has significant losses.
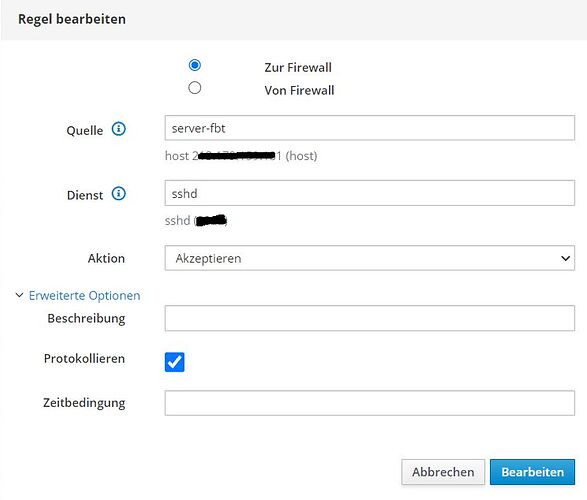
Now I have created a local rule on each server to give the other server access to the SSHD service via the fixed IP.
Question:
It is limited to only one IP address at a time, should the port still be closed again after copying or is that still safe?
The speed is 1:1 what the line is capable of.
I am also considering releasing the proxy service with this.
Greetings and thanks
Nicky
Translated with www.DeepL.com/Translator (free version)
Hi @supernicky
All forms of VPN do use overhead.
I tend to use IPsec for Site2Site VPNs and OpenVPNs for RoadWarriors.
I will be using Wireguard more in future, considering its advantages…
IPsec, in my experience tends to “scale” better than OpenVPN, especially for regular, large volume data-syncs (eg off site backups).
A lot of factors can and do play an issue:
- Type of data (compressed or not, or already pre-compressed, eg MP3 or JPG.
- CPU Power on both ends doing the actual encryption, nowadays less use off CPU-Offloading with external encryption hardware…
- Type of line/link and capacity
- Fixed or dynamic IPs (Impact on security!)
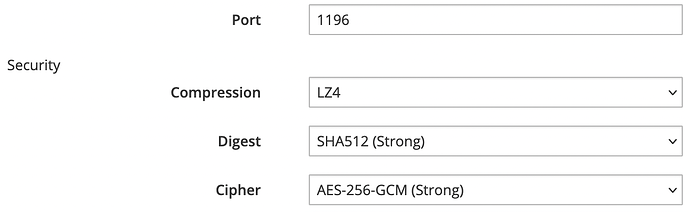
- Used encryption, nowadays, the following is geerally best practices with OpenVPN and IPsec: SHA512, AES-256-GCM (This one alone improves ca 30-40% compared to its AES256 predecessor!)…
An interesting comparison of thruput using OpenVPN and Wireguard…
A site2site VPN, with at least one side using static IP (even better is both sides using static IPs) offers much more security than a SSH connection, simply as the port is always occupied, any other IPs can be locked out.
Not only for SSH, but you should have Fail2ban on both sides!
My 2 cents
Andy
I use mainly OPNsense as firewall, and therefore VPN Endpoint, but I do have one NethServer in the cloud doing OpenVPN. My settings:
2 Likes