Hello, I am on NS v7.4 and currently have a working pfsense box. When I quickly look at NS’s QoS, I thought it is not as “strong” as pfsense. I do not know enough to compare each function side by side but just a feeling when I skim the doc. Can someone tell me if NS QoS is better/worse/same as pfsense?
I can speak for NethServer.
We don’t shape (i.e. limit) traffic, we prioritize it trying to always use all the available bandwidth.
We use a vanilla shorewall simple traffic shaping setup:
http://shorewall.org/simple_traffic_shaping.html
I would like to move to shorewall complex shaping to take advantage of codel (but I have a patch for codel on simple shaping). I also have a test setup with complex shaping and hfsc.
To take an informed decision I would like to make comprehensive tests. If somebody here could run Flent (https://flent.org/) on a variety of internet links I will provide test material.
Any time … but I can and will not use nethserver as firewall due to how that would impact our production.
I would need a maintenance weekend to use nethserver for those tests. Read; not any time soon.
I DO have 2 pfsense appliances running … with an ipsec site to site between them, an openvpn road warrior setup and a bunch of site to sites with customers.
I have no issue stress testing that in off hours 
If you want to test a more advanced traffic shaping using codel (http://shorewall.net/traffic_shaping.htm) follow this steps:
yum --enablerepo=nethserver-testing update nethserver-firewall-base
config setprop firewall tc Internal
signal-event firewall-adjust
Look for code in shorewall show tc output to confirm activation. Example output:
#shorewall show tc | grep codel
qdisc fq_codel 3: parent 1:11 limit 10240p flows 1024 quantum 1514 target 5.0ms interval 100.0ms ecn
qdisc fq_codel 4: parent 1:12 limit 10240p flows 1024 quantum 1514 target 5.0ms interval 100.0ms ecn
qdisc fq_codel 5: parent 1:13 limit 10240p flows 1024 quantum 1514 target 5.0ms interval 100.0ms ecn
I suggest using flent on ubuntu following bufferbloat.net instructions. Please test buffer bloat before and after update.
@alefattorini, do you think that this deserves a separate topic?
Nope, I think that it’s ok here.
You can always opt for a dedicated Gateway role on a separate NS instance. Then your other services are not affected by NS gateway service.
True, but still be behind a pfsense firewall … and that would not work too well in a comparison.
Hi,
Are you still looking for testers?
I tried following the recipe but “yum” found no packages to update.
These are my current version:
# rpm -qa|fgrep nethserver-firewall-base nethserver-firewall-base-ui-3.2.11-1.ns7.noarch nethserver-firewall-base-3.2.11-1.ns7.noarch
Thx!
Yes, I’m still looking for testers. I’m working on yet another setup, I will update this topic when everything is ready for testing (next week, I’m on vacation now).
Hi Filippo,
I hope you enjoyed your vacation.
Do things still look like you might have some bits to be tested this week or would it be for next week?
My environment:
- 120 Mbps down / 20 mbps up
- Five homes sharing the Internet
- Slight limitation, some of our wireless backbone is only 100 Mbps
- We use Zabbix to monitor ICMP vs WAN Throughput
Thx!
I still have some problems with mark-based traffic classification. I need some time, sorry.
No need to apologize, you are help us! 
I’ll stand by until I hear from you.
Thank you for working on this feature. I appreciate it!
Hi Filippo,
Have you had a chance to look into the mark-based traffic classification or is it a tough problem to solve?
As I don’t want to be a pest, would you prefer I just wait for an update to the thread or to periodically ping you. 
Thank you!
-pablo
I have completed my tests over the weekend.
It has been an amusing full immersion experience.
The good news is that I achieved all targets.
The bad news is that we need RHEL 7.5, so the release is delayed for at least a couple of months, probably a bit more.
On the other hand, I’m using an improved QoS configuration in production and it seems to work better than the standard one.
I plan to ask for merging of this improved version
Would you like to test it using 2 custom templates?
Hi Flippo,
Is RHEL 7.5 truly needed or can CentOS be used?
I’d love to test the two custom templates but CentOS 7.5 is not released. Hmmm. What do I need to do in order to test them?
Thank you!
-pablo
CentOS 7.5 will be fine (when released), but it’s not yet available, so I had to use RHEL 7.5 beta1 for the tests.
The custom templates will only enable fq_codel which behaves better than sfq.
Give me some hours to create a package.
It sounds as if I will have to patch the O/S on my NethServer 7.4.1708 eh?
Thx!
-pablo
I have built updated packages.
Temporary instructions:
yum update http://packages.nethserver.org/nethserver/7.4.1708/autobuild/x86_64/Packages/nethserver-firewall-base-3.3.1-1.5.pr60.g12598d4.ns7.noarch.rpm http://packages.nethserver.org/nethserver/7.4.1708/autobuild/x86_64/Packages/nethserver-firewall-base-ui-3.3.1-1.5.pr60.g12598d4.ns7.noarch.rpm
config setprop firewall tc Internal
signal-event firewall-adjust
I suggest setting ingress (inbound/download) bandwidth to empty or zero. If you put a limit on ingress (why?), you may need to disable advanced features on some ethernet cards.
ethtool -K $IF tso off
ethtool -K $IF gso off
Substitute $IF with the wan (red) interface name.
Hi Filippo,
I am currently running the latest bits. Thank you!
I have some data.
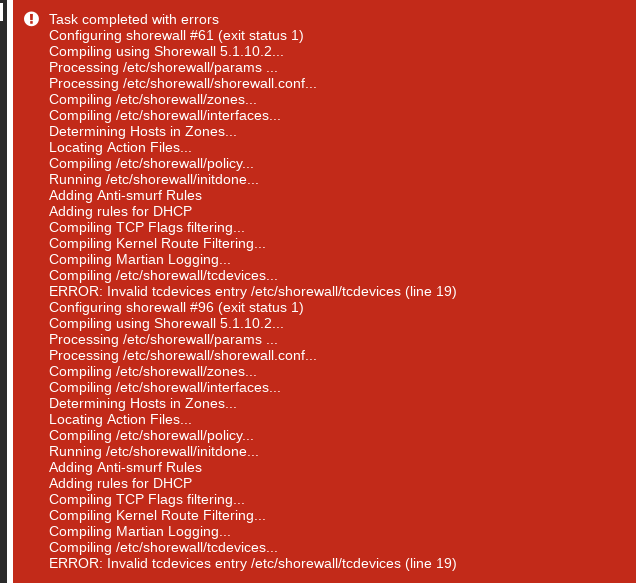
Bug
If I clear out outbound bandwidth (blank) as well, I get an error[1]. The gateway also fails to forward packets.
If I reset the outbound bandwidth, the gateway resumes forwarding packets.
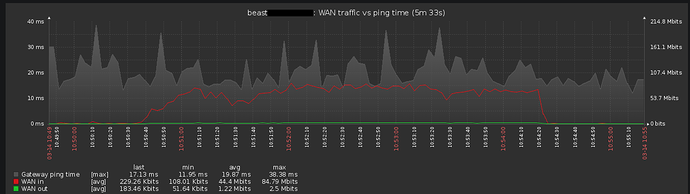
Stress Test
I ran a stress test where I downloaded an ISO at full speed. In parallel, I made a VoIP call. I didn’t run a full-on ping test but I captured some ping data[2] - subsequent post. The ping is to my ISP’s gateway.
The results of the test were promising but not perfect. 
The phone conversation was noticeably affected by the download. When I paused the download, all was well. Basically I could hear the other party but there were times when the call was a bit choppy.
References
[1] - setting outbound bandwidth to (blank) too: