here we eat piadina, only pizza rossini are eventually accepted
We are working hard
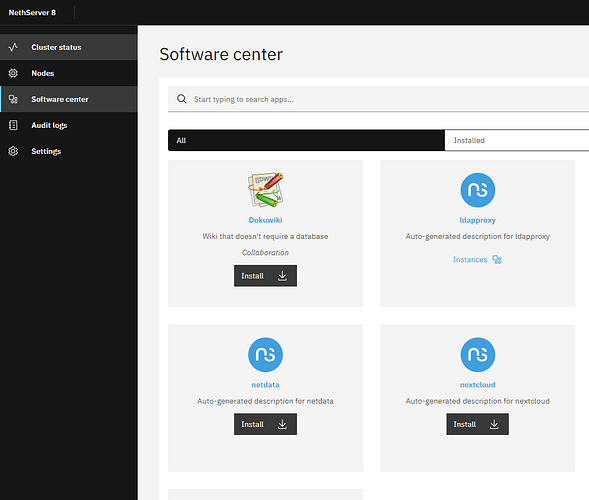
Future SMB / SME server in the making.
I just f…![]() … love you guys!
… love you guys!
![]()
![]()
![]()
![]()
![]()
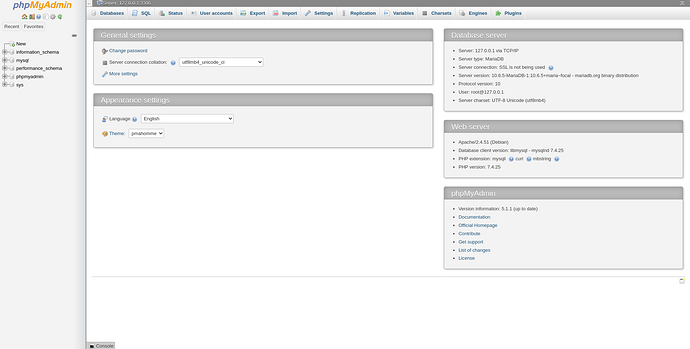
Just done a new module for ns8…mariadb 10.6.5 and phpmyadmin inside a podman pod
[mariadb1@fedora ~]$ podman ps -a
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
3cefb4f28ce3 k8s.gcr.io/pause:3.5 26 minutes ago Up 26 minutes ago 127.0.0.1:20009->80/tcp, 0.0.0.0:3306->3306/tcp c4ee9aefa2cd-infra
b819ecd45aae docker.io/library/mariadb:10.6.5 --character-set-s... 26 minutes ago Up 26 minutes ago 127.0.0.1:20009->80/tcp, 0.0.0.0:3306->3306/tcp mariadb-app
f4fe64ca5bb8 docker.io/library/phpmyadmin:5.1.1 apache2-foregroun... 26 minutes ago Up 26 minutes ago 127.0.0.1:20009->80/tcp, 0.0.0.0:3306->3306/tcp phpmyadmin-app
Done on NS8 during my nethesis week event, thank to all the team and also dedicated to @davidep @giacomo and @filippo_carletti for their hospitality. I think I won’t forget it for a while.
We are close to go to take a beer…
yeah, seems its taking shape now…
cool that modules are starting to take shape.
Since everything is docker based, then this tool should come as default installable.
The idea is not only to run container but run container rooless (more secure) and started by a systemd service owned by a simple (linux) user
Podman can generate a template of systemd service to start the pod (therefore the containers inside it), so it exists a lot of helpers for developers
The concept of pod is smart, it is a kind of container that runs other containers inside so they can talk together by the 127.0.0.1:tcp_port or eventually by a linux socket.
After that you decide to export tcp ports outside of the pod or not, all fqdn are handled by traefik that creates automatically an internal tcpport for that pod and make a route between this fqdn to that tcp port (binded to localhost for security)
The big interest for example when I do a rpm for dokuwiki is that you can install it just one time in a server, with the containers you can have several dokuwiki instances on the same server (obviously with different fqdn to reach them). The cons is that for each instance of dokuwiki you need 400MB of disk place because a container is also an operating system itself.
thats the challenge with containers. Also saw something about persistency of containers.
ok am new to this container work of docker k8 and the tools podman etc. and now even traefik. there is alot to unplug
About containers, a couple of noob questions:
-
Will NS8 still be able to be installed as a VM? (KVM in particular)
-
Assuming we can. Do the containers need to be hosted by NS8 itself? Or can they be hosted by NS8’s own host somehow? (and sharing networking or something)
Yes kvm is fine
NS8 will start and stop pod of podman containers by systemd. Most of container will be rootless (owned by a linux user) few will be rootfull because they need to mount a special file system (it is a shortcut because rootless could do it also)
After that you decide to open tcp/udp ports outside of the pod or not.
For my scratch mariadb module we expose only 3306 tcp outside of the pod, like you can open the mariadb port when you install it on ns7
You can also create for your need one mariadb container inside each pod and share the 127.0.0.1 of the pod to all containers inside this pod.
NS8 could be compared to a (light) kubernete cluster
Definitely sounds promising.
I hope we see it in the next 12 months.
I installed a new Debian11 today in proxmox and then ran the script from ns8-scratchpad. It went through without any problems. After that I created a cluster with the command “create-cluster nethsrv8.intra.dmz:55820 10.5.4.0/24 Nethesis,1234”. The VM was then restarted.
I am unable to connect to “https://nethsrv8.intra.dmz/cluster-admin/”.
netstat -ano gave as output:
Aktive Internetverbindungen (Server und stehende Verbindungen)
Proto Recv-Q Send-Q Local Address Foreign Address State Timer
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN aus (0.00/0/0)
tcp 0 0 10.5.4.1:20008 0.0.0.0:* LISTEN aus (0.00/0/0)
tcp 0 0 10.5.4.1:6379 0.0.0.0:* LISTEN aus (0.00/0/0)
tcp 0 0 127.0.0.1:6379 0.0.0.0:* LISTEN aus (0.00/0/0)
tcp 0 0 127.0.0.1:8080 0.0.0.0:* LISTEN aus (0.00/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36176 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 192.168.20.70:22 192.168.20.30:33366 VERBUNDEN keepalive (6881,07/0/0)
tcp 0 0 127.0.0.1:36168 127.0.0.1:6379 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:36176 127.0.0.1:6379 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 10.5.4.1:20008 10.5.4.1:39546 VERBUNDEN keepalive (7,41/0/0)
tcp 0 0 127.0.0.1:36182 127.0.0.1:6379 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 10.5.4.1:39546 10.5.4.1:20008 VERBUNDEN keepalive (7,41/0/0)
tcp 0 0 127.0.0.1:36188 127.0.0.1:6379 VERBUNDEN aus (0.00/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36170 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36182 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36188 VERBUNDEN keepalive (86,78/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36168 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36186 VERBUNDEN keepalive (86,78/0/0)
tcp 0 0 192.168.20.70:22 192.168.20.30:33362 VERBUNDEN keepalive (6876,31/0/0)
tcp 0 0 127.0.0.1:36170 127.0.0.1:6379 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:36186 127.0.0.1:6379 VERBUNDEN aus (0.00/0/0)
tcp 0 64 192.168.20.70:22 192.168.20.30:33685 VERBUNDEN ein (0,23/0/0)
tcp 0 0 127.0.0.1:36178 127.0.0.1:6379 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:36172 127.0.0.1:6379 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36172 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36166 VERBUNDEN keepalive (286,77/0/0)
tcp 0 0 127.0.0.1:36166 127.0.0.1:6379 VERBUNDEN keepalive (286,76/0/0)
tcp 0 0 127.0.0.1:6379 127.0.0.1:36178 VERBUNDEN keepalive (286,76/0/0)
tcp6 0 0 :::22 :::* LISTEN aus (0.00/0/0)
tcp6 0 0 ::1:6379 :::* LISTEN aus (0.00/0/0)
tcp6 0 0 :::80 :::* LISTEN aus (0.00/0/0)
udp 0 0 0.0.0.0:55820 0.0.0.0:* aus (0.00/0/0)
udp6 0 0 :::55820 :::* aus (0.00/0/0)
Aktive Sockets in der UNIX-Domäne (Server und stehende Verbindungen)
…
I am missing port 80 on IPv4.
What can I do?
@rosi_steiner Did you try it with the IP of your debian installation?
=> https://xxx.xxx.xxx.xxx/cluster-admin/
For me it works. 
Hi guys,
I was curious and installed NS8 on a fedora 35 vm in proxmox.
After some installation of some devel-tools it ran through the script like a charm.
So far so good.
Keep working on it! You are great my friends!! 
check that you have no firewall, I ran the same issue on fedora
systemctl disable --now firewalld
It was not the firewall.
I am now reinstalling Debian11 again and starting from scratch. Then it should work.
I don’t know what I’m doing wrong.
Installation with Debian11 Netinstall: The installation goes through, but the domain is not reachable.
Installation with Fedora 35 (Workstation and Server) Error while processing the script.
Requirement already satisfied: setuptools in /usr/local/agent/pyenv/lib/python3.10/site-packages (from jsonschema==3.2.0->-r /etc/nethserver/pythonreq.txt (line 29)) (59.2.0)
Using legacy ‘setup.py install’ for cchardet, since package ‘wheel’ is not installed.
Using legacy ‘setup.py install’ for cffi, since package ‘wheel’ is not installed.
Using legacy ‘setup.py install’ for hiredis, since package ‘wheel’ is not installed.
Using legacy ‘setup.py install’ for ipcalc, since package ‘wheel’ is not installed.
Using legacy ‘setup.py install’ for pycares, since package ‘wheel’ is not installed.
Using legacy ‘setup.py install’ for psutil, since package ‘wheel’ is not installed.
Building wheels for collected packages: aiohttp, multidict, yarl, pyrsistent
Building wheel for aiohttp (pyproject.toml) … done
Created wheel for aiohttp: filename=aiohttp-3.7.4.post0-py3-none-any.whl size=451944 sha256=855bccda50d785d3a9a0e5e827b7814da9c94da3f59268036dc0f37b69864e72
Stored in directory: /root/.cache/pip/wheels/fc/84/e0/52113c57eb9b09b6b187a0f369eaad6fc7fc64bb7247c83b89
Building wheel for multidict (pyproject.toml) … error
ERROR: Command errored out with exit status 1:
command: /usr/local/agent/pyenv/bin/python /usr/local/agent/pyenv/lib64/python3.10/site-packages/pip/_vendor/pep517/in_process/in_process.py build_wheel /tmp/tmpr0guwhl6
cwd: /tmp/pip-install-0kdgypn/multidict_87c6306acc144138ace63eb0b30c5cf8
Complete output (48 lines):
- Accelerated build *
running bdist_wheel
running build
running build_py
creating build
creating build/lib.linux-x86_64-3.10
creating build/lib.linux-x86_64-3.10/multidict
copying multidict/_multidict_py.py → build/lib.linux-x86_64-3.10/multidict
copying multidict/_multidict_base.py → build/lib.linux-x86_64-3.10/multidict
copying multidict/_compat.py → build/lib.linux-x86_64-3.10/multidict
copying multidict/_abc.py → build/lib.linux-x86_64-3.10/multidict
copying multidict/init.py → build/lib.linux-x86_64-3.10/multidict
running egg_info
…
My EYES!!! ARRRGGGHHHH!!!
I made it work with Debian, and looks pretty good, but remeber: KISS, the actual NS7 interface es perfect!!
Cheers!!
The installation then still worked. I had to reinstall some packages that my freshly installed Fedora35 did not have.
ok, can someone here explain to me properly what kubernetes is. in Nethserver speak.
its getting confusing now. if its a platform for managing docker or container applications, then what is portainer, is it not Kubernetes also.
am sorry if this question sounds so simplistic. i really need to understand and all videos and articles i come accros just go straight to action and i become even more lost…
maybe others are also facing a similar issue but afraid to ask.
As with editors, webservers and many other common tools in Linux, there are many tools covering more or less the same spectrum.
There are several tools for handling Docker style containers - just as NethServer has SoGo, WebTop and NextCloud for handling Groupware.
It’s up to you, your requirements and what your required apps require.
My 2 cents
Andy
so docker and kubernetes are not brothers. they are totally diferrent.