This is more of a general musing and rant, but anyone can feel free to throw in their 2 pence along the way.
The first time I tried Suricata was on a VM testing out a new version of Zentyal, which is what I ran then as my edge/firewall machine, before they started dropping components like hot potatoes. Shortly after starting it I wondered why repsonse times seemed sluggish. I guess the solid 100% CPU it was using might be causing that. A couple of attempts at tweaking it didn’t seem to do anything, so it soon was dropped from the installed list.
After switching to NS from Zentyal, the flavour of the month for IPS was snort. This I ran until I found that it was throttling my internet connection down from 200 Mbit/s down to around 85 Mbit/s. So that got turned off.
Sometime after NS switched from Snort to Suricata, I thought I’d give it a try again, despite my experiences with Zentyal. Happily the massive CPU hit didn’t materialise again. So, I was a happy camper, at least for a while, although I did notice that copying files from my internal LAN to a Samba shared hosted on NS did run like a snail was hand carrying the bytes one-by-one, accompanied by a massive CPU hit. But as most of the time that was happening was during the early hours, when my backups were running, I could live with it.
Then at the beginning of the year, there was a change in some of the rules that bit me hard by blocking a huge number of websites and VPNs, and judging by some of the posts here, I wasn’t the only one. At the time, it was pointed out that I should be selective about the rules used and the actions taken for each rule. Like anyone, other than the developers of the rules, really understands every nuance about what rules to use with what actions. So, again, I turned off IPS.
As part of the responses to my, ond other, post, both Filippo and Giacomo suggested the rule set that NS itself was using. So, a couple of weeks ago I restarted Suricata using that rule set.
After a couple of days, I noticed that a Microsoft automatic update, for the Office products, was being blocked. Maybe that’s not a bad thing, as some folks do think that this is a form of virus/malware anyway. Then last week, I noticed that my daily backup from my RedHat laptop to a share on NS had stopped working. While investigating this, I found I could no longer connect to a Samba share on NS from either my RH laptop, or a Slackware VM. The CIFS mount command was accepted, but never completes. Further digging revealed that, yes, yet again, Suricate was the issue by blocking part of the connection.
I guess that was the last straw and now Suricata if off for good. Unless anyone can convice me otherwise that it does more good that the hassles it causes.
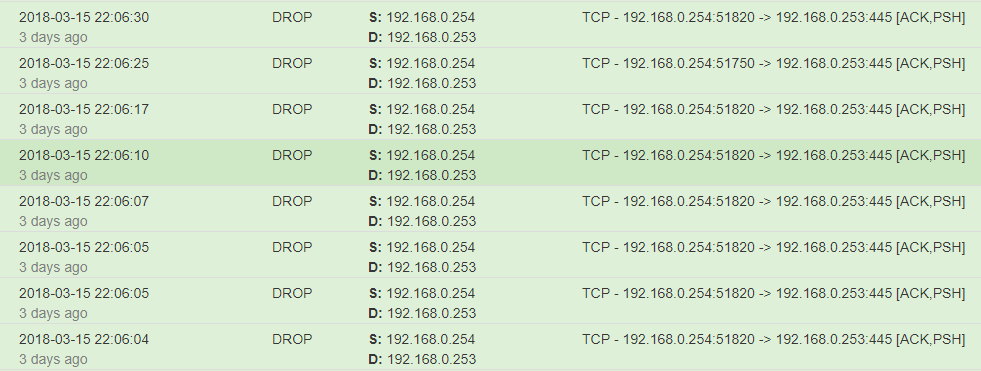
Oh, and by the way, it also throws this out as well:
254 is NS, and 253 is the Samba DC. So it’s getting it’s sticky little fingers in the way there as well.
</Rant>
Cheers.