This is my routing table.
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
default gateway 0.0.0.0 UG 0 0 0 enp2s0
link-local 0.0.0.0 255.255.0.0 U 1002 0 0 enp2s0
link-local 0.0.0.0 255.255.0.0 U 1003 0 0 enp3s0
link-local 0.0.0.0 255.255.0.0 U 1004 0 0 enp4s5
link-local 0.0.0.0 255.255.0.0 U 1005 0 0 enp4s5.1
172.20.1.0 0.0.0.0 255.255.255.0 U 0 0 0 enp2s0
172.31.3.0 0.0.0.0 255.255.255.0 U 0 0 0 enp3s0
172.31.4.240 172.31.4.242 255.255.255.240 UG 0 0 0 tunrw
172.31.4.242 0.0.0.0 255.255.255.255 UH 0 0 0 tunrw
172.31.110.0 0.0.0.0 255.255.255.0 U 0 0 0 enp2s0
172.31.253.0 0.0.0.0 255.255.255.248 U 0 0 0 enp4s5.1
172.31.254.0 0.0.0.0 255.255.255.0 U 0 0 0 enp4s5
Would you please post yours?
A bug on the interface has been found on OpenVPN subnetting validation
Give us a try using a /24 subnet will help us find another bug on IpSec.
Is one of the subnets used in another network segment on one of two sites?
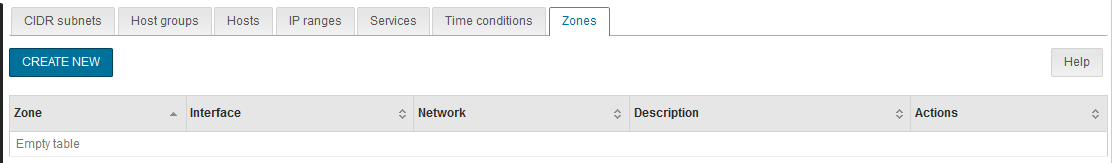
Also… Zones?
I did not add any zone on my firewall interface.