Download and Install
To start with, we need to download the latest version of PowerBroker Identity Services from GitHub
Also, you can download it by simply running following command on Ubuntu OS:
wget https://github.com/BeyondTrust/pbis-open/releases/download/8.5.3/pbis- open-8.5.3.293.linux.x86.deb.sh
Now, you need to set execution bit and execute the package with root privileges:
chmod +x pbis-open-8.5.3.293.linux.x86_64.deb.sh
sudo ./pbis-open-8.5.3.293.linux.x86_64.deb.sh
It will ask a couple of question during installation so choose options accordingly. Once the installation is done its time to join the machine to the domain.
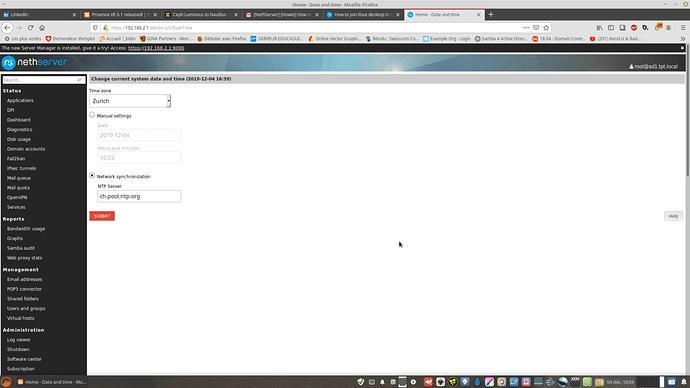
PBIS Configuration
We are ready to proceed with configuration. Please navigate to /opt/pbis/bin/ directory and run domainjoin-cli command to join a host to an Active directory domain.
cd /opt/pbis/bin/
sudo domainjoin-cli join [DomainName [DomainAccount]
sudo domainjoin-cli join ad.tpt.local administrator
where,
DomainName - the name of your domain
DomainAccount - your domain account (user@domainname)
Example: sudo domainjoin-cli join example.com administrator
When prompted, please provide Active Directory administrator’s password.
on error joining ad do;
sudo apt-get remove avahi-daemon
sudo domainjoin-cli join example.com administrator
sudo apt-get install avahi-daemon
et reboot
sudo pam-auth-update
reboot
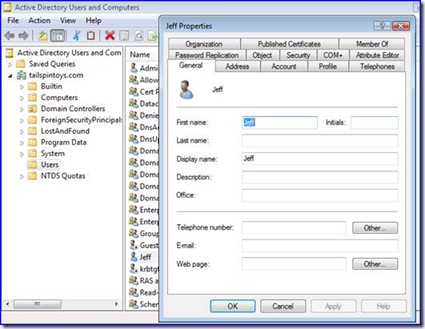
On successful authentication, the command adds your Ubuntu computer as a member of the domain. The command also adds entries in the /etc/hosts file.
To check Ubuntu domain setting you need to run the following command from your terminal:
sudo domainjoin-cli query
The command will display the name of the domain to which your Ubuntu computer has joined.
Example:
Name = username
Domain = example.com
Distinguished Name = CN=username,CN=Computers,DC=example,DC=com
Note: If you want to remove your Ubuntu computer from the domain, you need to run
sudo domainjoin-cli leave
Once joined to the domain important thing to do is to restrict access to sudoers group to members of Domain Admin group only. This can be accomplished by updating /etc/sudoers file by adding %domain^admins ALL=(ALL) ALL in group section so sudoers file section looks as follows:
Members of the admin group may gain root privileges
%admin ALL=(ALL) ALL
%domain^admins ALL=(ALL) ALL
The good thing about using PBIS is that it allows multiple ways to customize the login, domain prefix, login shell, folder name, etc. In order to set up default configuration for domain users, you need to use PBIS to set the environment for all required domain users that will be logged to the system.
Please open the terminal and run following commands:
sudo /opt/pbis/bin/config UserDomainPrefix [Domain]
Set domain prefix
sudo /opt/pbis/bin/config AssumeDefaultDomain True
Set this to ‘true’ avoid entering domain names all the time
sudo /opt/pbis/bin/config LoginShellTemplate /bin/bash
Set default shell
sudo /opt/pbis/bin/config HomeDirTemplate %H/%D/%U
Set different home dir then the local users on the machine
sudo /opt/pbis/bin/config RequireMembershipOf "[Domain]\[SecurityGroup]"
Set specific Active Directory security groups
Next step, you need to edit the pamd.d common-session file. Please type in terminal:
sudo vi /etc/pam.d/common-session
Navigate to the line that states session sufficient pam_lsass.so and replace it with session [success=ok default=ignore] pam_lsass.so
Then, we need to edit the lightdm configuration file and append the following lines:
sudo vi /usr/share/lightdm/lightdm.conf.d/50-unity-greeter.conf
allow-guest=false
greeter-show-manual-login=true
Please note, that if you are using Lubuntu 14.04 your lightdm configuration file will be 60-lightdm-gtk-greeter.conf
issue login not permited but it sees users