NethServer Version: 7.9
I tried to upgrade my GLPI-Server with:
yum --enablerepo=* clean all && yum update -y
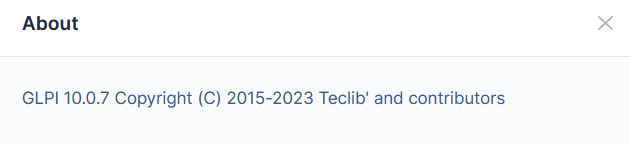
The GLPI-Url shows me this:
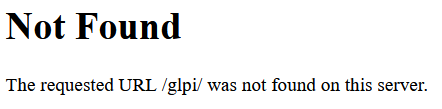
If I use the Upgrade-Button I get this:
How can I fix it?
NethServer Version: 7.9
I tried to upgrade my GLPI-Server with:
yum --enablerepo=* clean all && yum update -y
The GLPI-Url shows me this:
If I use the Upgrade-Button I get this:
How can I fix it?
I was able to update GLPI with these commands:
cd /usr/share/glpi/
php81 bin/console glpi:maintenance:enable
yum --enablerepo=* clean all && yum update -y
php81 bin/console database:update
php81 bin/console migration:utf8mb4
php81 bin/console migration:unsigned_keys
php81 bin/console glpi:maintenance:disable
php81 bin/console glpi:database:enable_timezones
But there is just (hopefully) only one last thing:
How should I change the Web server root directory configuration for GLPI?
oups sorry I forgot this one, you upgraded from what version ? I see now it glp10
to make it disappear you have to use a virtual host, let me check the doc
OK, tnx in advise…
config setprop glpi DomainName glpi.ns7loc2.org
signal-event nethserver-glpi-10-latest-update
sorry for the delay, next time please ping me by the @stephdl, just a lot of things to do, I am quite confident that a signal-event nethserver-glpi-10-latest-update could have fixed the issue
If I use these commands:
With my own DomainName (FQDN) I get this error:
normal you must use glpi.ns7loc2.org to reach your glpi instance and obviously this FQDNmust exists locally or globally on your DNS provider
Do you mean I have to setup a DNS entry who points from glpi.ns7loc2.org to my GLPI-Server-IP?
yes if you want to remove this warning you have to use a virtualhost and use it so fully yes you need to have this FQDN that points to your glpi IP
And If not, is it insecure or just a matter of cosmetic?
just because they want to avoid people who install with a chmod 777 -R but trust me it is not
I know this may be off topic but you just reminded me of a script I created (unfortunately I lost it during a server rebuild and completely forgot to backup it up) that was run as a hook esmith custom template.
Basically after creating a virtual host it would use cloud flare api to create an a record and wait 5 minutes (to allow for DNS propagation) and then trigger the let’s encrypt certificate generation.
I need to check but here the vhost use the default certificate of ns7 hence it could be LE or self created by the server
This why I use git and github everywhere even on servers to save my life