Hi
I’m using a similiar setup for a Hotel, we only have about 12 cameras at the moment, but more are planned.
I’m using mrmarkuz setup described here:
One problem you may run into is that reverse-proxy can’t correctly handle just forwarding something like:
http://nethserver.cdomain.com/cam01/, and say http://nethserver.cdomain.com/cam02/, as the actual target gets redirected to a folder /view/ (At least for the Axis cams we’re using here…), which would also have to be entered as a redirect. That would only work for one camera…
My solution was to create external DNS entries for all cameras in the form:
http://cam01.mydomain.com
http://cam02.mydomain.com
and so on…
all pointing to the external adress of my clients Nethserver.
The NethServer has no such entries, only normal A-entries for each camera in it’s DNS.
The actual redirecting of domains is done using mrmarkuz how-to above…
This is working now for all cameras!
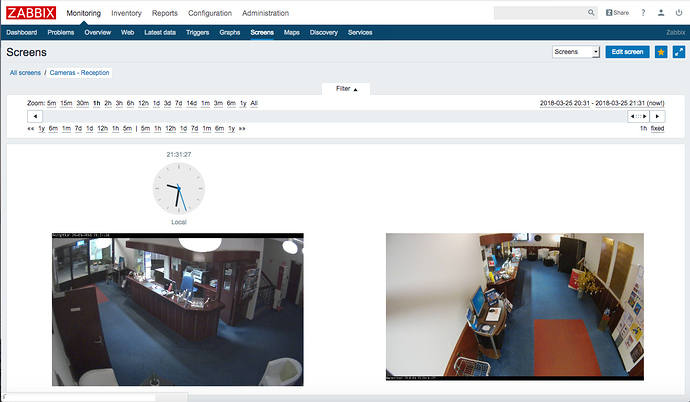
This image shows 2 cameras (Hotel-Reception) inside Zabbix, another Project running in NethServer! This monitors all systems here, including cameras…
My 2 cents, including a hat-tip to mrmarkuz for his great work!
Andy