**NethServer Version:7.5
**Module:SMTP Proxy
Hello
Please recommend how to block spam mail Sender = Recipient like a from abc@domain.com to abc@domain.com
Thank you
**NethServer Version:7.5
**Module:SMTP Proxy
Hello
Please recommend how to block spam mail Sender = Recipient like a from abc@domain.com to abc@domain.com
Thank you
In rspamd web interface go to symbols and add a score to “TO_EQ_FROM” (just search for “from to”, I sorted by score after setting it to 30 to get a smaller screenshot) symbol and click “Save”:
I used score 30 for testing (score over 20 will be rejected) and if I try to send an email in roundcube with same from and to then the message is rejected:
In /var/log/maillog:
Dec 11 00:28:51 testserver rspamd[15743]: <ffbe9a>; proxy; rspamd_task_write_log: id: <cd4ae12709e254ed087597860ab872a8@domain.local>, qid: <1FA4E103EF8E>, ip: 127.0.0.1, from: <markus@domain.local>, (default: T (reject): [29.90/20.00] [TO_EQ_FROM(30.00){},MIME_GOOD(-0.10){text/plain;},FROM_EQ_ENVFROM(0.00){},FROM_NO_DN(0.00){},MID_RHS_MATCH_FROM(0.00){},MIME_TRACE(0.00){0:+;},RCPT_COUNT_ONE(0.00){1;},RCVD_COUNT_ZERO(0.00){0;},RCVD_TLS_ALL(0.00){},TO_DN_NONE(0.00){},TO_MATCH_ENVRCPT_ALL(0.00){}]), len: 362, time: 13.071ms real, 5.714ms virtual, dns req: 0, digest: <47f00803e89be0f2ffb6cab29a0e01c3>, rcpts: <markus@domain.local>, mime_rcpts: <markus@domain.local>
Dec 11 00:28:51 testserver rspamd[15743]: <ffbe9a>; proxy; rspamd_protocol_http_reply: regexp statistics: 0 pcre regexps scanned, 0 regexps matched, 181 regexps total, 0 regexps cached, 0B bytes scanned using pcre, 0B bytes scanned total
Dec 11 00:28:51 testserver postfix/cleanup[16366]: 1FA4E103EF8E: milter-reject: END-OF-MESSAGE from localhost[127.0.0.1]: 5.7.1 Spam message rejected; from=<markus@domain.local> to=<markus@domain.local> proto=ESMTP helo=<192.168.1.187>
@mrmarkuz
Thank you so much
Other issue Sometime the [Envelope From] From show only “@” like as shown below:
ID IP Address [Envelope From] From [Envelope to] To/Cc/Bcc Subject
undef 192.185.149.105 [] @ my-email@domain.com Your Mailbox Account Login Error Message! Unlock Now.
What 's web interface go to symbols to score for Headers show only “@” ?
Thank you
Other question about spam block, if I would like blocked some email send to [Envelope To] To/Cc/Bcc "xyz@domain.com"
Thank you
It seems this is not implemented yet but you may create a custom template:
mkdir -p /etc/e-smith/templates-custom/etc/rspamd/local.d/multimap.conf
cat > /etc/e-smith/templates-custom/etc/rspamd/local.d/multimap.conf/90blacklistto <<EOF
local_bl_rcpt \{ type = "rcpt"; map = "\$LOCAL_CONFDIR/local.d/local_bl_rcpt.map.inc"; symbol = "LOCAL_BL_RCPT"; description = "Local rcpt blacklist";score = 3;\}
EOF
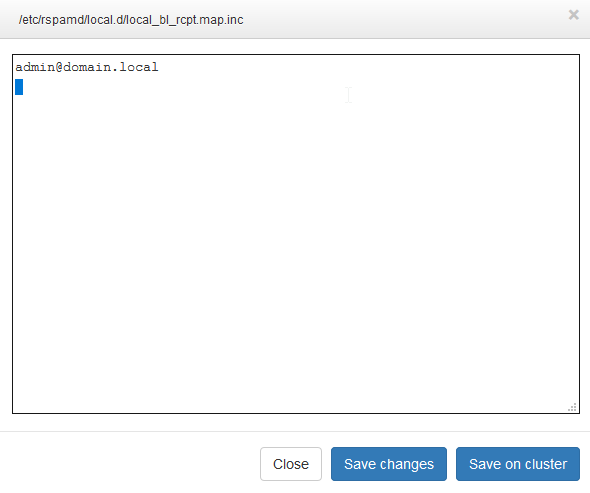
touch /etc/rspamd/local.d/local_bl_rcpt.map.inc
chmod o+w /etc/rspamd/local.d/local_bl_rcpt.map.inc
expand-template /etc/rspamd/local.d/multimap.conf
systemctl restart rspamd
Now you have a new list “Local rcpt blacklist” where you can enter recipient addresses to block.
Don’t forget to put a newline after each mail address else it will not work.
Source:
Thank you so much @mrmarkuz
Hi @Ya_Ley.
could you please mark this thread as solved.
Hello @mrmarkuz
I am not sure the RSPAMD can filter Phishing or not ? because sometime there are some email passing the RSPAMD
Thank you again.
Nethserver rspamd uses phishtank, see /etc/rspamd/modules.d/phishing.conf
https://rspamd.com/doc/modules/phishing.html
You may try to enable openphish but I didn’t test…
Hello @mrmarkuz
phishing {
symbol = “PHISHING”;
# Disabled by default
openphish_enabled = true;
openphish_premium = false;
openphish_map = “https://www.openphish.com/feed.txt”;
# Disabled by default
phishtank_enabled = true;
# Make exclusions for known redirectors
redirector_domains = [
"https://maps.rspamd.com/rspamd/redirectors.inc.zst:REDIRECTOR_FALSE",
"$LOCAL_CONFDIR/local.d/redirectors.inc:LOCAL_REDIRECTOR_FALSE",
"fallback+file://${CONFDIR}/redirectors.inc:REDIRECTOR_FALSE"
];
.include(try=true,priority=5) "${DBDIR}/dynamic/phishing.conf"
.include(try=true,priority=1,duplicate=merge) "$LOCAL_CONFDIR/local.d/phishing.conf"
.include(try=true,priority=10) "$LOCAL_CONFDIR/override.d/phishing.conf"
}
systemctl restart rspamd
is it correct ?
Thank you
Hello
I don’t understand why some senders there are mult i[Envelope From] From like as shown below
[bounce-mc.us15_74134406.203691-myname=mydomain.com@mail6.atl31.mcdlv.net] owxxxxx@gmail.com
and I can not block because the domain gen auto mail6.atl31.mcdlv.net , mail6.atlxxx.mcdlv.net
How to block multi sender header ?
Thank you
It’s ok for testing. If it works you should write the settings to /etc/rspamd/override.d/phishing.conf to not change default settings of rspamd that could be overwritten in future:
http://docs.nethserver.org/en/v7/rspamd.html#modify-the-settings-of-a-module
I found a thread with a similar problem, the solution seems to be the bayes filter.
Hello
After I have update to 7.6 then I try to use tool “Free Email Security Check”
https://www.emailsecuritycheck.net/index.html
The Result some mail passed, it mean, it can not block the attachment
Please advice
I’m getting “Email spoofing” of email messages with a forged sender address;
how can I block email from x@mydomain.com to y@mydomain.com, without blocking the internal sending?
maybe you can block from postfix before rspamd?
An SPF record can help. Rspamd evaluates it and can block mails sent from servers that are not allowed.
And should help a lot not only your server, but also the whole internet.
I activated the spf record on the dns (-all), in rspamd I set R_SPF_FAIL to 30 instead of default 1, the reject works, but can there be problems?
I’ve been using -all for years and haven’t had any problems. The only important thing is that all servers that are allowed to send e-mails are also listed in the SPF Record. I didn’t set a high value in Rspamd, that’s normally enough. The situation is different with ~all, where it can make sense to increase the value.
but if not increased the value in Rspamd does not reject