Run the following commands:
cp /etc/krb5.conf /etc/krb5.conf.orig
sed -i 's/includedir/#includedir/' /etc/krb5.conf
diff -u /etc/krb5.conf.orig /etc/krb5.confRun the following commands:
cp /etc/krb5.conf /etc/krb5.conf.orig
sed -i 's/includedir/#includedir/' /etc/krb5.conf
diff -u /etc/krb5.conf.orig /etc/krb5.conf— /etc/krb5.conf.orig 2016-12-13 10:02:44.247340581 +0100
+++ /etc/krb5.conf 2016-12-13 10:02:53.767187443 +0100
@@ -1,5 +1,5 @@
-includedir /etc/krb5.conf.d/
+#includedir /etc/krb5.conf.d/
[logging]
default = FILE:/var/log/krb5libs.log
Ok now try again the “Domain accounts” page…
NetBIOS domain name: COMPU-MAX
ads_connect: No logon servers
ads_connect: No logon servers
Didn’t find the ldap server!
ads_connect: No logon servers
Join to domain is not valid: No logon servers
ads_connect: No logon servers
ads_connect: No logon servers
My krb5.conf looks identical to @hucky 's.
[root@ns7test samba]# cat /etc/krb5.conf
# Configuration snippets may be placed in this directory as well
includedir /etc/krb5.conf.d/
[logging]
default = FILE:/var/log/krb5libs.log
kdc = FILE:/var/log/krb5kdc.log
admin_server = FILE:/var/log/kadmind.log
[libdefaults]
dns_lookup_realm = false
ticket_lifetime = 24h
renew_lifetime = 7d
forwardable = true
rdns = false
# default_realm = EXAMPLE.COM
default_ccache_name = KEYRING:persistent:%{uid}
[realms]
# EXAMPLE.COM = {
# kdc = kerberos.example.com
# admin_server = kerberos.example.com
# }
[domain_realm]
# .example.com = EXAMPLE.COM
# example.com = EXAMPLE.COM
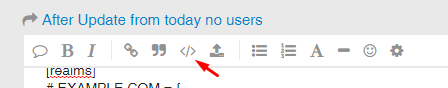
Just a hint for Kai: if you format the copied text with this (red arrow) you get it like mine above.
Much better to read 
after a reboot i got this:
NetBIOS domain name: COMPU-MAX
LDAP server: 192.168.100.1
LDAP server name: nsdc-sbs.compu-max.lan
Realm: COMPU-MAX.LAN
Bind Path: dc=COMPU-MAX,dc=LAN
LDAP port: 389
Server time: Di, 13 Dez 2016 11:30:42 CET
KDC server: 192.168.100.1
Server time offset: 0
Last machine account password change: Fr, 21 Okt 2016 13:25:00 CEST
kerberos_kinit_password SBS$@COMPU-MAX.LAN failed: Preauthentication failed
kerberos_kinit_password SBS$@COMPU-MAX.LAN failed: Preauthentication failed
Join to domain is not valid: Logon failure
kerberos_kinit_password SBS$@COMPU-MAX.LAN failed: Preauthentication failed
kerberos_kinit_password SBS$@COMPU-MAX.LAN failed: Preauthentication failed
kerberos_kinit_password SBS$@COMPU-MAX.LAN failed: Preauthentication failed
kerberos_kinit_password SBS$@COMPU-MAX.LAN failed: Preauthentication failed
but it seems to change after a few minutes into the status that the domain is not existent.
sql is up and ldap service is also up.
in system overview i got
for my understanding this:
kerberos_kinit_password SBS$@COMPU-MAX.LAN failed: Preauthentication failed
kerberos_kinit_password SBS$@COMPU-MAX.LAN failed: Preauthentication failed
Join to domain is not valid: Logon failure
is the main problem, but i dont get something what to do… it is a known problem then and when, also at red hat side but did not find something where a solution is written down.
We didn’t found the origin of the problem, and I can’t reproduce it!
We could try to manually re-join the domain… First, leave it:
realm leave compu-max.lan
Some clean ups:
systemctl stop sssd
find /var/lib/sss/ -name '*.ldb' -delete
> /etc/sssd/sssd.conf
systemctl stop realmd
signal-event nethserver-dnsmasq-save
Join it again
realm join compu-max.lan
…at prompt, type the administrator password, then
signal-event nethserver-sssd-savethanks a lot, this has worked !!!
After successful migration of our F-Secure server to NethServer machine I decided to Install all updates from “Software center”. There were many of them, but all went smooth. Next thing I noticed after reboot were empty user list (create new user was working fine), broken login to SOGo, and chat. In “Domain accounts” there were errors just like @hucky reported.
@davidep solution resolved my problem. Thanks
Hi Guys!
It’s going to tear your hair - it goes on!
Today I have the problem that my users have disappeared and the message AccountProvider_Error_1 appears, ok - no problem the guidance is yes in the forum.
Everything works so far, except for one I have changed the admin password and not recorded.
Therefore, I can not complete the command realm join domainname.
Where is this confused password stored in the system?
HELP
Thanks greetings
Gerald
If you’re running a local Samba DC account provider, to enable and reset administrator’s password:
systemd-run -t -M nsdc /bin/bash
samba-tool user enable administrator
samba-tool user setpassword administrator --newpassword=Nethesis,1234
And also
It supports -U flag, to specify an alternative user with domain join rights. For instance
realm join -U admin
This issue seems related to this bug