Yep its nice and getting better and better.
I wouldn’t say that OpenVPN is very bad 
I would choose it anytime over IPSec.
You wrote :
“Its very easy to set up a personal server, all we would need is a proper front-end on nethserver. Very exciting development in VPN’s!”
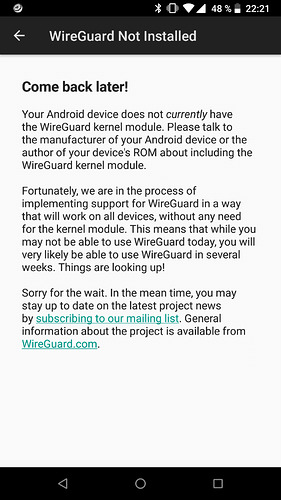
Last time i had difficulties on CentOS 7
But it’s getting there and looks very promising.
How does one build a front-end on Nethserver ?
I have already set up many wireguard tunnels its not even hard  its super easy !
its super easy !
First you need to install the wireguard module and the wireguard-tools userland utilites .
Make sure it is working properly.
As i said last time i tried it i had problem on CentOS 7.
Lack of time to test on Nethserver 
On the server side you need to have ip forwarding enabled.
$ nano /etc/sysctl.conf
net.ipv4.ip_forward=1
$ sysctl -p
$ mkdir /etc/wireguard/
$ cd /etc/wireguard
$ wg genkey | tee server-private.key | wg pubkey > server-public.key
$ nano /etc/wireguard/wg0.conf
[Interface]
Address = 192.168.199.1/24
ListenPort = 51820
PostUp = iptables -A FORWARD -i wg0 -j ACCEPT; iptables -t nat -A POSTROUTING -o NIC1 -j MASQUERADE
PostDown = iptables -D FORWARD -i wg0 -j ACCEPT; iptables -t nat -D POSTROUTING -o NIC1 -j MASQUERADE
PrivateKey = SERVER_PRIVATE_KEY
SaveConfig = true
[Peer]
PublicKey = CLIENT_PUBLIC_KEY
AllowedIPs = 192.168.199.2/32
$ chmod 700 server-*.key /etc/wireguard/wg0.conf
$ wg-quick up wg0
$ wg show
On the client side :
$ mkdir /etc/wireguard
$ cd /etc/wireguard
$ wg genkey | tee client-private.key | wg pubkey > client-public.key
$ nano /etc/wireguard/wg0.conf
[Interface]
Address = 192.168.199.2
PostUp = echo UP
PostDown = echo DOWN
PrivateKey = CLIENT_PRIVATE_KEY
[Peer]
PublicKey = SERVER_PUB_KEY
AllowedIPs = 0.0.0.0/0
Endpoint = PUBLIC_VPN_IP:51820
$ chmod 700 client-*.key /etc/wireguard/wg0.conf
$ wg-quick up wg0
$ wg show
And it is easy as that to set up a wireguard vpn
You can throw wg genpsk into the mix to make it even more secure.
Then just add that as PresharedKey = on both sides to the INTERFACE part.
Also be sure to change NIC1 to your eth0 or whatever your Network Interace is on the server.
Adding new clients its as easy as with one.
Just keep adding clients to the server config and create new clients as above.
https://git.zx2c4.com/WireGuard/about/src/tools/wg.8
edit : you must enter the long keys into the wg0.conf file , i just stored them for later use or for whatever reason 
![]()

 its super easy !
its super easy !