And @davidep
I have uploaded a copy of maillog to my personal ftp server: ftp dot bogolinux dot net. Anonymous download is allowed.
POP3 Proxy is used, for all intent and purposes, for all emails.
Cheers.
And @davidep
I have uploaded a copy of maillog to my personal ftp server: ftp dot bogolinux dot net. Anonymous download is allowed.
POP3 Proxy is used, for all intent and purposes, for all emails.
Cheers.
Mar 11 08:24:58 Nethserver clamd[6181]: SelfCheck: Database status OK.
Mar 11 08:27:50 Nethserver rspamd[5964]: <acc2a9>; csession; rspamd_controller_check_password: allow unauthorized connection from a trusted IP 127.0.0.1
Mar 11 08:27:50 Nethserver rspamd[5964]: <acc2a9>; csession; rspamd_mime_text_to_utf8: converted from ISO_8859-1:1987 to UTF-8 inlen: 139, outlen: 139
Mar 11 08:27:50 Nethserver rspamd[5964]: <acc2a9>; csession; rspamd_message_parse: loaded message; id: <4B5E45DB5D50C0C3D6CD53D5D8484B5E@3G14F9O9R5>; queue-id: <undef>; size: 1364; checksum: <f1cb9215a3a0bfeb70373548a2c14525>
Mar 11 08:27:50 Nethserver rspamd[5964]: <acc2a9>; csession; fuzzy_generate_commands: <4B5E45DB5D50C0C3D6CD53D5D8484B5E@3G14F9O9R5>, part is shorter than 1000 bytes: 278 (139 * 2.00 bytes), skip fuzzy check
Mar 11 08:27:50 Nethserver rspamd[5964]: <acc2a9>; csession; fuzzy_generate_commands: <4B5E45DB5D50C0C3D6CD53D5D8484B5E@3G14F9O9R5>, part is shorter than 1000 bytes: 278 (139 * 2.00 bytes), skip fuzzy check
Mar 11 08:27:53 Nethserver rspamd[5964]: <acc2a9>; lua; url_redirector.lua:161: found redirect from https://goo.gl/TdmLYP to http://trustinfomarket.su/?157977032, err code 301
Mar 11 08:27:53 Nethserver rspamd[5964]: <acc2a9>; surbl; surbl_continue_process_handler: <4B5E45DB5D50C0C3D6CD53D5D8484B5E@3G14F9O9R5> got reply from redirector: 'https://goo.gl/TdmLYP' -> 'http://trustinfomarket.su/?157977032'
Mar 11 08:27:53 Nethserver rspamd[5964]: <acc2a9>; surbl; process_dns_results: <4B5E45DB5D50C0C3D6CD53D5D8484B5E@3G14F9O9R5> domain [trustinfomarket.su.dbl.spamhaus.org] is in surbl dbl.spamhaus.org(201007f)
Mar 11 08:27:57 Nethserver rspamd[5964]: <acc2a9>; csession; bayes_classify: skip classification as ham class has not enough learns: 37, 200 required
Mar 11 08:27:57 Nethserver rspamd[5964]: <acc2a9>; csession; rspamd_task_write_log: id: <4B5E45DB5D50C0C3D6CD53D5D8484B5E@3G14F9O9R5>, ip: 102.158.229.231, from: <ness@samsun.co.kr>, (default: T (reject): [32.60/20.00] [DBL_SPAM(6.50){trustinfomarket.su.dbl.spamhaus.org;},SPAM_FLAG(5.00){},ONCE_RECEIVED_STRICT(4.00){},RBL_SPAMHAUS_XBL_ANY(4.00){},MX_INVALID(3.00){},HFILTER_HOSTNAME_UNKNOWN(2.50){},MX_MISSING(2.00){query timed out;},RBL_SPAMHAUS_CSS(2.00){231.229.158.102.zen.spamhaus.org : 127.0.0.3;},RBL_SPAMHAUS_PBL(2.00){231.229.158.102.zen.spamhaus.org : 127.0.0.11;},RDNS_NONE(1.00){},MID_RHS_NOT_FQDN(0.50){},DMARC_POLICY_SOFTFAIL(0.10){samsun.co.kr : No valid SPF, No valid DKIM;none;},MIME_GOOD(-0.10){text/plain;},ONCE_RECEIVED(0.10){},ASN(0.00){asn:37705, ipnet:102.158.0.0/16, country:TN;},DIRECT_TO_MX(0.00){Microsoft Windows Live Mail 16.4.3505.912;},FREEMAIL_ENVRCPT(0.00){attglobal.net;},FREEMAIL_TO(0.00){attglobal.net;},FROM_EQ_ENVFROM(0.00){},FROM_HAS_DN(0.00){},HAS_X_PRIO_THREE(0.00){3;},PREVIOUSLY_DELIVERED(0.00){eddie_atherton@attglobal.net;},RCPT_COUNT_ONE(0.00){1;},RCVD_COUNT_ONE(0.00){1;},RCVD_NO_TLS_LAST(0.00){},RECEIVED_SPAMHAUS(0.00){231.229.158.102.zen.spamhaus.org;},R_DKIM_NA(0.00){},R_SPF_NA(0.00){},TO_DN_NONE(0.00){}]), len: 1364, time: 7314.034ms real, 14.160ms virtual, dns req: 28, digest: <f1cb9215a3a0bfeb70373548a2c14525>, mime_rcpt: <eddie_atherton@attglobal.net>
Mar 11 08:37:50 Nethserver clamd[6181]: SelfCheck: Database status OK.Mar 11 08:27:57 Nethserver rspamd[5964]: <acc2a9>; csession; rspamd_protocol_http_reply: regexp statistics: 76 pcre regexps scanned, 3 regexps matched, 163 regexps total, 7 regexps cached, 5.88k bytes scanned using pcre, 5.88k bytes scanned total
Mar 11 08:41:57 Nethserver postfix/smtpd[29331]: connect from unknown[36.66.238.11]
this is the full logs, I do not understand the first line…it is likely pop3 proxy bypass the postfix milter @davidep ???
yep pop3 proxy is the target
Mar 12 08:48:06 Nethserver postfix/anvil[12079]: statistics: max cache size 1 at Mar 12 08:41:32
Mar 12 08:51:06 Nethserver rspamd[5964]: <7c231d>; csession; rspamd_controller_check_password: allow unauthorized connection from a trusted IP 127.0.0.1
Mar 12 08:51:06 Nethserver rspamd[5964]: <7c231d>; csession; rspamd_message_parse: loaded message; id: <0.1.1F.E1A.1D3BA19E0E30C7C.0@drone184.ral.icpbounce.com>; queue-id: <undef>; size: 46467; checksum: <b6fdcc470eb57d2df95f9969cf8a61ab>
Mar 12 08:51:07 Nethserver rspamd[5964]: <7c231d>; surbl; process_dns_results: <0.1.1F.E1A.1D3BA19E0E30C7C.0@drone184.ral.icpbounce.com> domain [icptrack.com] is in surbl uribl.rspamd.com
Mar 12 08:51:07 Nethserver rspamd[5964]: <7c231d>; surbl; process_dns_results: <0.1.1F.E1A.1D3BA19E0E30C7C.0@drone184.ral.icpbounce.com> domain [icptrack.com.multi.uribl.com] is in surbl multi.uribl.com(4)
Mar 12 08:51:08 Nethserver rspamd[5964]: <7c231d>; surbl; process_dns_results: <0.1.1F.E1A.1D3BA19E0E30C7C.0@drone184.ral.icpbounce.com> domain [icontact.com.multi.uribl.com] is in surbl multi.uribl.com(4)
Mar 12 08:51:10 Nethserver rspamd[5964]: <7c231d>; csession; bayes_classify: skip classification as ham class has not enough learns: 106, 200 required
Mar 12 08:51:10 Nethserver rspamd[5964]: <7c231d>; csession; rspamd_task_write_log: id: <0.1.1F.E1A.1D3BA19E0E30C7C.0@drone184.ral.icpbounce.com>, ip: 207.254.213.241, from: <bounces@icpbounce.com>, (default: F (rewrite subject): [6.80/20.00] [RAMBLER_URIBL(4.50){icptrack.com;},URIBL_GREY(1.50){icptrack.com.multi.uribl.com;icontact.com.multi.uribl.com;},R_DKIM_REJECT(1.00){icontactmail3.com;},MV_CASE(0.50){},MX_GOOD(-0.50){bounces001.icpbounce.com;},R_SPF_ALLOW(-0.20){+ip4:207.254.213.192/26;},MIME_GOOD(-0.10){multipart/alternative;text/plain;},ONCE_RECEIVED(0.10){},ASN(0.00){asn:7349, ipnet:207.254.208.0/20, country:US;},DMARC_NA(0.00){seasmoke.com;},FREEMAIL_ENVRCPT(0.00){attglobal.net;},FREEMAIL_TO(0.00){attglobal.net;},FROM_HAS_DN(0.00){},FROM_NEQ_ENVFROM(0.00){customerservice@seasmoke.com;bounces@icpbounce.com;},HAS_REPLYTO(0.00){customerservice@seasmoke.com;},PREVIOUSLY_DELIVERED(0.00){eddie_atherton@attglobal.net;},RCPT_COUNT_ONE(0.00){1;},RCVD_COUNT_ONE(0.00){1;},RCVD_IN_DNSWL_NONE(0.00){241.213.254.207.list.dnswl.org : 127.0.15.0;},RCVD_NO_TLS_LAST(0.00){},REDIRECTOR_FALSE(0.00){seasmoke->click.icptrack.com;},REPLYTO_ADDR_EQ_FROM(0.00){},RWL_MAILSPIKE_GOOD(0.00){241.213.254.207.rep.mailspike.net : 127.0.0.18;},TAGGED_FROM(0.00){656879.14961151.875882;},TO_DN_NONE(0.00){}]), len: 46467, time: 3262.015ms real, 22.761ms virtual, dns req: 67, digest: <b6fdcc470eb57d2df95f9969cf8a61ab>, mime_rcpt: <Eddie_Atherton@attglobal.net>
Mar 12 08:51:10 Nethserver rspamd[5964]: <7c231d>; csession; rspamd_protocol_http_reply: regexp statistics: 112 pcre regexps scanned, 1 regexps matched, 163 regexps total, 7 regexps cached, 144.61k bytes scanned using pcre, 144.61k bytes scanned total
Mar 12 09:00:38 Nethserver postfix/smtpd[12679]: connect from unknown[185.234.216.190]
no where the postfix milter is invocated after the transaction
if you use the smtp of your server (with a webmail on your server for instance) , can you send the spam string I posted to you ?
can you post your full configuration file for /etc/p3scan/p3scan.conf please
well Houston we have a problem…p3scan use
spamcheck=/usr/bin/rspamc -h localhost:11334 --mime
thinking loudly, maybe the headers added are not the same expected by p3scan
https://rspamd.com/doc/integration.html#lda-mode
The doc states no rejection is possible…the changelog of p3scan give us the last update : 2007
Just in case you still need it:
[root@Nethserver ~]# grep -v ^# /etc/p3scan/p3scan.conf
maxchilds = 250
user = p3scan
scanner = /usr/bin/clamdscan --no-summary --config-file=/etc/clamd.d/rspamd.conf --fdpass
virusregexp = .*: (.*) FOUND
broken
checkspam
spamcheck=/usr/bin/rspamc -h localhost:11334 --mime
subject = [VIRUS]
template = /etc/p3scan/p3scan-en.mail
[root@Nethserver ~]#
Is this still needed. Because I’m not quite sure what you’re asking for. Do you want me to send an email to my server with that string. Or try and send one out.
Old software never dies. ![]()
Update Sorry, I forgot to add, that it appears that P3Scan is still doing it’s job with regard to emails that it thinks are a Virus (even though most are really only Spam) by replacing the body.
Cheers.
well, old softwares have no maintainers and are opened to issues and outages…with the milter filter nowadays you talk directly to your MTA (postfix), no more need for this ![]()
both, send you an email directly with the webmail, test rspamd without p3scan
Which is fine for folks who have the email address for my own domain, but not the ones who only have my original (20 year old) hosted email.
Attempting to send via NS:
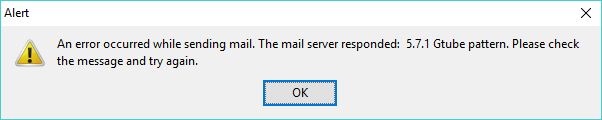
Sending from gmail, directly to NS:
Mar 12 15:07:07 Nethserver postfix/smtpd[23879]: connect from mail-wr0-f175.google.com[209.85.128.175]
Mar 12 15:07:07 Nethserver rspamd[5963]: <2218b5>; proxy; proxy_accept_socket: accepted milter connection from /var/run/rspamd/worker-proxy port 0
Mar 12 15:07:08 Nethserver postfix/smtpd[23879]: 4528E10422D2: client=mail-wr0-f175.google.com[209.85.128.175]
Mar 12 15:07:08 Nethserver rspamd[5963]: <2218b5>; milter; rspamd_milter_process_command: got connection from 209.85.128.175:38619
Mar 12 15:07:08 Nethserver postfix/cleanup[23884]: 4528E10422D2: message-id=<CAGVFP0EM9z6pDnSqwfnBevpXaaLWPmAXfanPOX8spoB8Lh9XUA@mail.gmail.com>
Mar 12 15:07:08 Nethserver rspamd[5963]: <2218b5>; proxy; rspamd_mime_part_get_cte: detected missing CTE for part as: 7bit
Mar 12 15:07:08 Nethserver rspamd[5963]: <2218b5>; proxy; rspamd_check_gtube: <CAGVFP0EM9z6pDnSqwfnBevpXaaLWPmAXfanPOX8spoB8Lh9XUA@mail.gmail.com>: gtube pattern has been found in part of length 95
Mar 12 15:07:08 Nethserver rspamd[5963]: <2218b5>; proxy; rspamd_check_gtube: <CAGVFP0EM9z6pDnSqwfnBevpXaaLWPmAXfanPOX8spoB8Lh9XUA@mail.gmail.com>: gtube pattern has been found in part of length 90
Mar 12 15:07:08 Nethserver rspamd[5963]: <2218b5>; proxy; rspamd_message_parse: loaded message; id: <CAGVFP0EM9z6pDnSqwfnBevpXaaLWPmAXfanPOX8spoB8Lh9XUA@mail.gmail.com>; queue-id: <4528E10422D2>; size: 3232; checksum: <f34985438e5f72b57a347b4c97b0e85d>
Mar 12 15:07:08 Nethserver rspamd[5963]: <2218b5>; proxy; rspamd_task_write_log: id: <CAGVFP0EM9z6pDnSqwfnBevpXaaLWPmAXfanPOX8spoB8Lh9XUA@mail.gmail.com>, qid: <4528E10422D2>, ip: 209.85.128.175, from: <xxxxxxxx@gmail.com>, (default: S (reject): [20.00/20.00] [GTUBE(0.00){}]), len: 3232, time: 0.000ms real, 0.358ms virtual, dns req: 0, digest: <f34985438e5f72b57a347b4c97b0e85d>, rcpts: <xxxxxxxx@bogolinux.net>, mime_rcpt: <xxxxxxxx@bogolinux.net>
Mar 12 15:07:08 Nethserver rspamd[5963]: <2218b5>; proxy; rspamd_protocol_http_reply: regexp statistics: 0 pcre regexps scanned, 0 regexps matched, 163 regexps total, 0 regexps cached, 0B bytes scanned using pcre, 0B bytes scanned total
Mar 12 15:07:08 Nethserver postfix/cleanup[23884]: 4528E10422D2: milter-reject: END-OF-MESSAGE from mail-wr0-f175.google.com[209.85.128.175]: 5.7.1 Gtube pattern; from=<xxxxxxxx@gmail.com> to=<xxxxxxxx@bogolinux.net> proto=ESMTP helo=<mail-wr0-f175.google.com>
Mar 12 15:07:08 Nethserver postfix/smtpd[23879]: disconnect from mail-wr0-f175.google.com[209.85.128.175]
Mar 12 15:07:08 Nethserver rspamd[5963]: <c74fad>; proxy; proxy_milter_finish_handler: finished milter connection
Nothing in the rspamd history though.
Cheers.
the two emails above were not written in history if I understand well, but they were rejected we agree on this ?
p3scan is the heart of the issue
IIUC when p3scan gets a message
Our clamd instance has also anti-malware DB signatures (phishing?) – it’s not only “anti-virus”.
@EddieA, could you spot the differences with the previous p3scan implementation based on rspamc? Did you notice any change compared to it?
Not in front of a computer, but with p3scan we have no dovecot instance running ?
Yes, p3scan is designed to run in a network gateway. The typical dovecot (mail-server) service runs in another host, but it does not matter.
Here the involved protocol is not IMAP, but POP3. POP3 clients in LAN connects remote POP3 servers; p3scan in the middle intercepts POP3 traffic and scan messages for viruses. It also add spam headers, but only clamd here decides what is blocked and what can pass.
Yes.
So what is “Reject” status, which I do see, if rejected mails are not added to the history.
Yes.
The Subject is no longer re-written for items that are deemed to be spam, but not caught by the AV check.
Cheers.
Could you paste here a couple of messages to test?
BTW we recently released rspamd 1.7.3: an update is available from the nethserver-updates repo!
How does that work with subscription updates. Wanted the karma from contributing to you guys for this software.
From: 55 2018 <>
X-Account-Key: account2
X-UIDL: 3694000029eb9b55
X-Mozilla-Status: 0000
X-Mozilla-Status2: 00000000
X-Mozilla-Keys:
Received-SPF: neutral (mail61c45.carrierzone.com: 190.51.200.197 is neither permitted nor denied by domain of CanadianBxfxhnuub@www.redlettercounsel.com) receiver=mail61c45.carrierzone.com; client-ip=190.51.200.197; helo=www.redlettercounsel.com; envelope-from=CanadianBxfxhnuub@www.redlettercounsel.com; x-software=spfmilter 2.001 http://www.acme.com/software/spfmilter/ with libspf2-1.2.10;
X-Envelope-From: CanadianBxfxhnuub@redlettercounsel.com
Return-Path: <CanadianBxfxhnuub@redlettercounsel.com>
Received: from www.redlettercounsel.com (190-51-200-197.speedy.com.ar [190.51.200.197] (may be forged)) by mail61c45.carrierzone.com (8.14.9/8.13.1) with ESMTP id w3I8hKvG003950 for <eddie_xxxxxxxx@xxxxxxxxxx.net>; Wed, 18 Apr 2018 04:43:26 -0400
Received: (qmail 12776 invoked by uid 11729); Wed, 18 Apr 2018 10:43:26 +0200
Date: Wed, 18 Apr 2018 10:43:26 +0200
Message-ID: <37825.7183.qmail@www.redlettercounsel.com>
Subject: Good Quality. You save up to 72%. New 14 products a week. Worldwide delivery.
Reply-To: CanadianBxfxhnuub@redlettercounsel.com
From: Canadian Express <CanadianBxfxhnuub@redlettercounsel.com>
To: eddie_xxxxxxxx@xxxxxxxxxx.net
X-Priority: 3
MIME-Version: 1.0
Content-Type: multipart/alternative; boundary="6d3c67b0853533e07f0f5a173e5ba3"
X-CTCH-Spam: Confirmed
X-Spam-Flag: YES
X-CTCH-VOD: Unknown
X-CTCH-RefID: str=0001.0A020205.5AD70514.0036,ss=4,sh,re=0.000,recu=0.000,reip=0.000,cl=4,cld=1,fgs=0
X-CSC: 100
X-CHA: v=2.2 cv=VrdTO6+n c=1 sm=1 tr=0 p=JPlc8rv7UMOAzdX9kUAA:9 p=UB6Ko0owtSQA:10 p=OsDqWU1mhLSGC5wCk6IA:9 a=qDHMczED3nHXsajNHeQ/qg==:117 a=qDHMczED3nHXsajNHeQ/qg==:17 a=Kd1tUaAdevIA:10 a=DAwyPP_o2Byb1YXLmDAA:9 a=3lYv5lZgAAAA:8 a=QEXdDO2ut3YA:10 a=y4wt1n_s0JA3uDbya0mI:22
X-WHL: LR
X-P3Scan: Version 2.3.2 by <laitcg@cox.net>/<folke@ashberg.de>
X-Spam-Scanner: rspamc 1.6.6
X-Spam-Scan-Time: 3.119
X-Spam: yes
X-Spam-Action: rewrite subject
X-Spam-Score: 12.40 / 20.00
X-Spam-Level: *************
X-Spam-Symbols: REPLYTO_ADDR_EQ_FROM,SPAM_FLAG,FROM_EQ_ENVFROM,RBL_SPAMHAUS_PBL, RCVD_NO_TLS_LAST,RCPT_COUNT_ONE,MID_RHS_WWW,R_SPF_NEUTRAL,DMARC_NA, TO_DN_NONE,PREVIOUSLY_DELIVERED,FREEMAIL_TO,FROM_HAS_DN,RCVD_COUNT_TWO, MX_INVALID,BAYES_SPAM,HAS_X_PRIO_THREE,ASN,MIME_GOOD,RECEIVED_SPAMHAUS, R_DKIM_NA,HAS_REPLYTO,FREEMAIL_ENVRCPT
Hello dear friend,
We have changed our domain and new link now is:
CLICK HERE
.
If the link is not active please copy this SAFE url to your browser:
http://www.redlettercounsel.com/xglvbqo.html
Thank you.
:
From: 28 2018 <>
X-Account-Key: account2
X-UIDL: 4194000029eb9b55
X-Mozilla-Status: 0000
X-Mozilla-Status2: 00000000
X-Mozilla-Keys:
X-Envelope-From: dannii@scu.edu.tw
Return-Path: <dannii@scu.edu.tw>
Received: from 178.90.228.19.megaline.telecom.kz (178.90.228.19.megaline.telecom.kz [178.90.228.19] (may be forged)) by mail78c45.carrierzone.com (8.14.9/8.13.1) with ESMTP id w3IGPFIL016761 for <eddie_xxxxxxxx@xxxxxxxxxx.net>; Wed, 18 Apr 2018 12:25:22 -0400
Message-ID: <4163F644B7D4D10527B200F390954163@ML31HH34>
From: errol acacia <dannii@scu.edu.tw>
To: eddie_xxxxxxxx@xxxxxxxxxx.net
Subject: Re:Medstore Online
Date: 19 Apr 2018 02:53:15 +0500
MIME-Version: 1.0
Content-Type: text/plain; charset="iso-8859-1"
Content-Transfer-Encoding: 7bit
X-Priority: 3
X-MSMail-Priority: Normal
Importance: Normal
X-Mailer: Microsoft Windows Live Mail 16.4.3505.912
X-MimeOLE: Produced By Microsoft MimeOLE V16.4.3505.912
X-CTCH-Spam: Confirmed
X-Spam-Flag: YES
X-CTCH-VOD: Unknown
X-CTCH-RefID: str=0001.0A020205.5AD77173.022B,ss=4,re=0.000,recu=0.000,reip=0.000,cl=4,cld=1,fgs=12
X-CSC: 100
X-CHA: v=2.2 cv=BM7DlBYG c=1 sm=1 tr=0 p=frSULwmOAAAA:20 a=1THfBVCcGqF/xHc2q3Wbpg==:117 a=1THfBVCcGqF/xHc2q3Wbpg==:17 a=8nJEP1OIZ-IA:10 a=x7bEGLp0ZPQA:10 a=3V0GumrZfryh4JHkkKoA:9 a=yM92gCOEL9jyUKB4VIBmhIlq6vk=:19 a=wPNLvfGTeEIA:10 a=UsUutX4Bi0IA:10 a=PzUWy4b0u10A:10 a=ddZT45GQ4RAA:10 a=zLnk64yTytkA:10 a=bqMFMFbQYbsA:10
X-WHL: LR
X-P3Scan: Version 2.3.2 by <laitcg@cox.net>/<folke@ashberg.de>
X-Spam-Scanner: rspamc 1.6.6
X-Spam-Scan-Time: 8.563
X-Spam: yes
X-Spam-Action: reject
X-Spam-Score: 23.58 / 20.00
X-Spam-Level: ************************
X-Spam-Symbols: RCVD_COUNT_ONE,SPAM_FLAG,DATE_IN_FUTURE,ONCE_RECEIVED, FROM_EQ_ENVFROM,RCVD_NO_TLS_LAST,HFILTER_URL_ONLY,RCPT_COUNT_ONE, MID_RHS_NOT_FQDN,DMARC_NA,TO_DN_NONE,RBL_SPAMHAUS_PBL,PREVIOUSLY_DELIVERED, FREEMAIL_TO,FROM_HAS_DN,RBL_SPAMHAUS_XBL_ANY,MX_GOOD,AUTH_NA,HAS_X_PRIO_THREE, R_SPF_NA,ASN,MIME_GOOD,URIBL_SBL,RECEIVED_SPAMHAUS,R_DKIM_NA,FAKE_REPLY, FREEMAIL_ENVRCPT
https://goo.gl/vKHqzR
Cheers.